
Targeted Ransomware and Data Exfiltration Attacks against Automotive Manufacturing Industry
Executive Summary
A threat actor operating under the alias "blinkzk" claimed responsibility for significant cyberattacks against two automotive manufacturing organizations — Royal Enfield and the Nevada Department of Motor Vehicles — reportedly becoming the perpetrator of a large-scale ransomware attack. The threat actor claimed to have encrypted all servers, deleted all backups, and set a 12-hour ransom ultimatum, threatening to auction the stolen data to third parties.
Incident Details
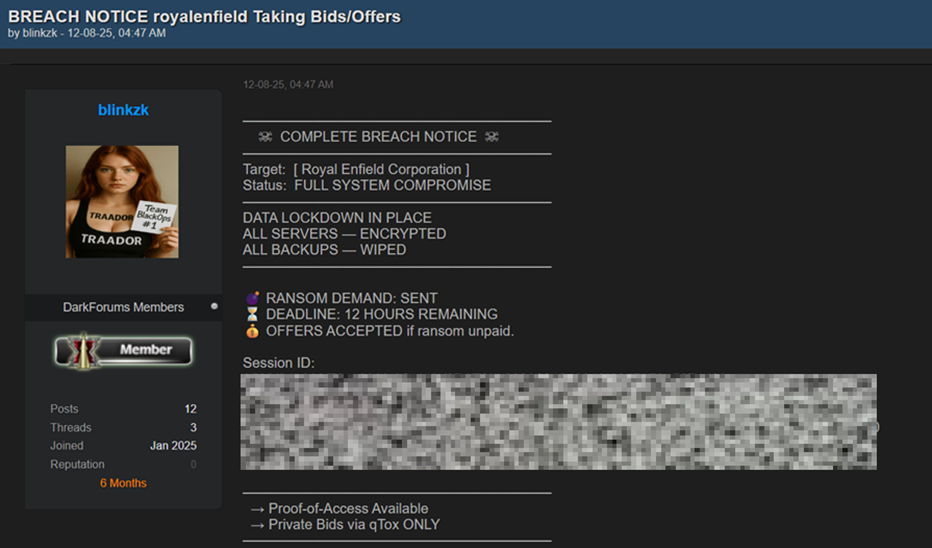
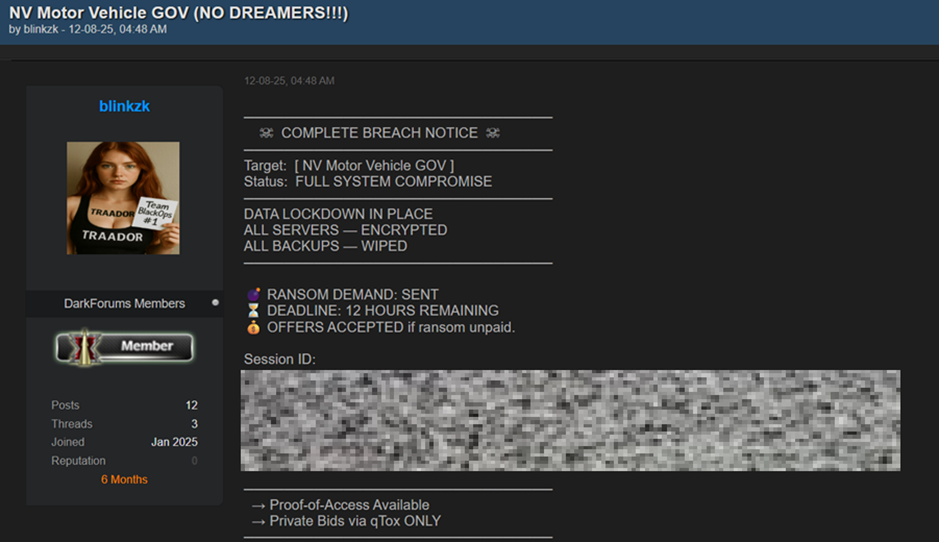
On 12th Aug’25, an undisclosed threat actor operating under the name “blinkzk” has published 2 back to back auction posts at the dark-forum about the complete breach of Royal Enfield (an Indian automotive company) and Nevada Department of Motor Vehicles (US based government automotive organization) respectively. Following are the redacted posts from the dark forum:
Breach Announcement of Royal Enfield:
Breach Announcement of NV Motor Vehicle GOV
Threat Actor Reputation:
The threat actor operating under the alias “blinkzk” is a registered member of the Dark Forums community, having joined in January 2025 and maintaining a presence for approximately six months as of August 2025. Their activity on the forum appears to be low to moderate, with a total of 12 posts and 3 threads created, suggesting that they focus on selective, high-impact engagements rather than frequent participation. The actor currently holds a reputation score of 0, indicating either a relatively new presence or limited community validation, though this does not necessarily diminish their operational capabilities. Their profile and posting history point towards targeted, high-stakes cybercriminal activities rather than broad, opportunistic operations.
Proof of Access Available claim:
The threat actor claims that “Proof-of-Access” is available, indicating they possess verifiable evidence of the alleged breach. However, despite this assertion, there has been no response from the actor over dark web instant messaging channels to validate the proof.
Though we couldn’t find any direct references, multiple security research blogs/news media posts mentioned that a spokesperson from Royal Enfield has officially acknowledged the breach and it is actively investigating the incident in collaboration with internal security teams and external incident response specialists to determine the full scope of the breach, the nature of the data accessed or exfiltrated, and the operational impact. While specific details regarding the stolen data have not yet been disclosed, Royal Enfield has confirmed that certain core business functions, including ordering systems and workshop services, have experienced disruption.
Technical Summary:
According to multiple published security research blogs, the breach was initiated through the exploitation of a zero-day vulnerability in Royal Enfield’s VPN gateway, serving as the initial access vector.
- Initial Access: Exploitation of a zero-day vulnerability in Royal Enfield’s VPN gateway.
- Lateral Movement: Post-compromise traversal across the corporate network to reach additional systems.
- Encryption Payload: Deployment of a custom AES-256-CBC encryption payload targeting live production systems.
- Data Destruction: Execution of the “Nuclear Wiper” malware via PowerShell to overwrite backups with random data prior to encryption, significantly reducing recovery options.
- Credential Harvesting: Use of Mimikatz to extract credentials from compromised systems.
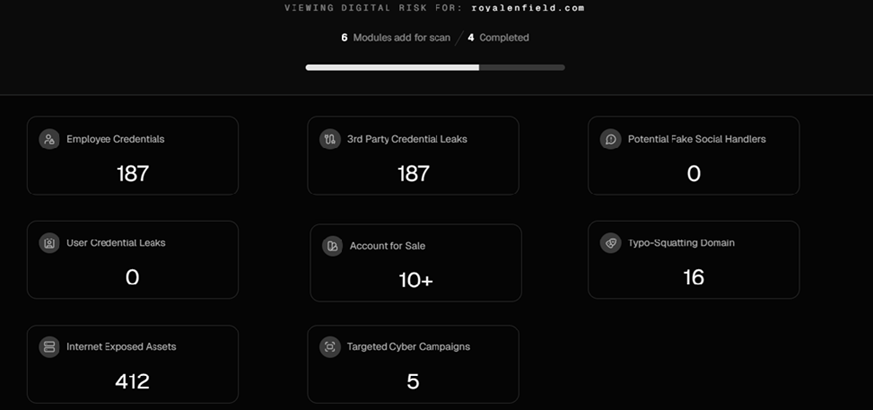
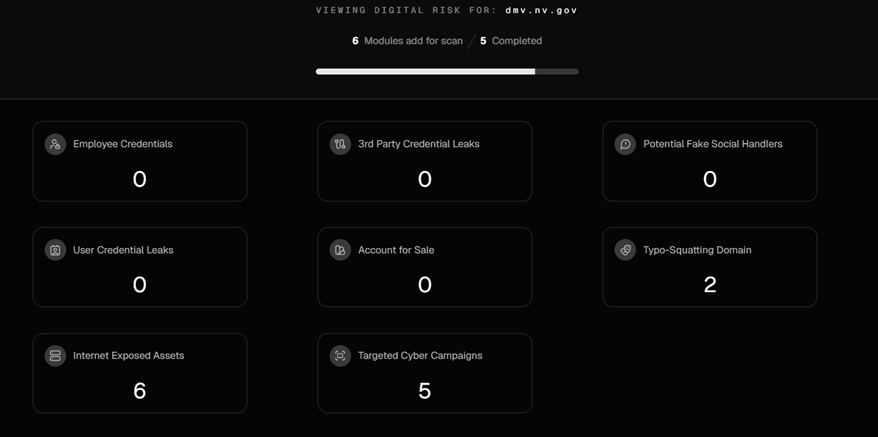
CyberXTron researchers, while attempting to triangulate the incidents by analysing the external exposure of both organizations, identified publicly accessible FTP applications running potentially outdated versions. In addition, our solution matched multiple dark web credential leaks associated with the domain, which could represent another possible initial access vector for exploitation. This observation remains part of our preliminary assessment. We will continue to monitor the situation and provide updates to this forum upon the release of official forensic findings from Royal Enfield following their breach investigation.
CyberXTron Live Risk Scan Results against “royalenfield.com”
CyberXTron Live Risk Scan Results against “dmv.nv.gov”
MITRE TTPs from the Incident Analysis:
| MITRE ATT&CK ID | Technique | Description |
| T1190 | Exploit Public-Facing Application | Exploitation of a zero-day vulnerability in Royal Enfield’s VPN gateway. |
| T1078 | Valid Accounts | Use of credentials from multiple dark web leaks associated with the domain. |
| T1133 | External Remote Services | Potential exploitation of publicly accessible, outdated FTP applications. |
| T1059.001 | Command and Scripting Interpreter: PowerShell | Execution of “Nuclear Wiper” malware via PowerShell. |
| T1570 | Lateral Tool Transfer | Movement of malicious tools/payloads across systems. |
| T1003.001 | OS Credential Dumping: Mimikatz | Harvesting credentials from compromised systems. |
| T1548 | Abuse Elevation Control Mechanism | Privilege escalation to gain administrative-level access. |
| T1486 | Data Encrypted for Impact | Deployment of AES-256-CBC encryption payload on live production systems. |
| T1490 | Inhibit System Recovery | Overwriting backups with random data before encryption. |
| T1561 | Disk Wipe | Nuclear Wiper malware deleting backup data. |
Indicator of Compromise:
The following IOCs are derived from the analysis of recent threat actor and ransomware campaigns targeting the manufacturing industry, along with the respective malware used in these targeted attacks.
|
Hash-MD5 |
Hash-Sha1 |
Hash-Sha256 |
|
73663c5164f1e73bfcd9b4c2bf79b0df |
bb79502d301ba77745b7dbc5df4269fc7b074cda |
3d117287a7806fb79ba57cac664d4e2d04056ad6ed47ced6dfd38f3bd29c2770 |
|
cfc116d5650415cd790489bda50c8ff5 |
0c3c878b678c7254446e84cca6f0d63caeb51880 |
0dbaf8970c0620e1b5902fd87c1cd0e72e917c45add84a024338c0481b5e161c |
|
827656f15b0a132b80e59bdbc2075bec |
77b294117cb818df701f03dc8be39ed9a361a038 |
12557dcf9c9a609521d7a2cc84a7e6fb95a93957aed6bda0f9644e96dfbbc180 |
|
6cef205923d8e00a680c6d6844b4509a |
be6ee00fa5284ee4237f877f4bd5cfa871fdc6ef |
20fe630a63dd1741ec4ade9fe05b2e7e57208f776d5e20bbf0a012fea96ad0c0 |
|
e8cf98899d62d18c410cf4225d0b0a98 |
79e19d3d8405425735e4b3cd36a8507d99dfee20 |
21614973732d4012889da2e1538b20fd1c0aefdb1d1452d79fd9a1bc06d569da |
|
3aadb3ff347cfbe733fba189f1e5a68a |
912217b09b13e1e53f7f26335f7f84b3c3918491 |
32ef3a0da762bc88afb876537809350a885bbbc3ec59b1838e9e9ccc0a04b081 |
|
f03e22d49115cff54e374e406165d501 |
8404521cf2a53de3459a75ff946873c43211afb6 |
34e347d1c9ce80b4e2b77f2de5aa7b4d98084704896bd169338c6d4b440e16c3 |
|
fd0da180f127f764074884c2ea301dee |
4a5852e9f9e20b243d8430b229e41b92949e4d69 |
3729396b11c69c60f9d096ce726f4cc5b4ed2054d89f7d195e998456de7fb229 |
|
79035b8d4d620fa41261c657b3187f87 |
Ed7c9fbd42605c790660df86b7ec325490f6d827 |
3b0772608844821555bb90e0218972f89f421dad9b1f7bd1918de26a929e998f |
|
2fbd8e6546303d4cc35550722d3c5b9a |
f32274eb1bb45fde2727565963b6e089cbb62e7f |
4bf4bcf1cc45d9e50efbd184aad827e2c81f900a53961cf4fbea90fa31ca7549 |
|
e0e23d82c9b74e41e16fc736943ec2d3 |
f28b87cfa94817cb45695be87b9a275cdbee71de |
50e5cd438024b34ba638e170f6e4595b0361dedb0ea925d06d06f68988468ddf |
|
e2e23dc6f4d374508f1cb6d6681a6d4c |
106248206f1c995a76058999ccd6a6d0f420461e |
53b85d1b7127c365a4ebae5f22ed479cd5d7e9efc716fb9df68ebdd18551834a |
|
194240ce935a6241755a49e4567e5a5b |
ea439ece0914972a29f3b3f7772e5e601165b6e5 |
544091acb5807aaac32ca4843bb85c4aa7ce0ab0acda296efa1a23fe3c181b7e |
|
3bfd7981b6c2f577a8e88ac49fb590dc |
411180c89953ab5e0c59bd4b835eef740b550823 |
5b51d1682cbd40cc6eca23333554ab16b7ed4bbd727712b3a00b07c24e629863 |
|
3737cc0b152f57618919f2d05504da3d |
4896cfff334f846079174d3ea2d541eec72690a0 |
5d16547900119112c12a755e099bed1fafe1890869df4db297a6a21ec40185b0 |
|
5ff1ba33d8807b90d03f2f989324a164 |
5ee4be6f82a16ebb1cf8f35481c88c2559e5e41a |
65fc84ffd9be05720b700292b7dbc0ac8afa7faaadf6fcd4485ce34785ba0932 |
|
01fb1ba006dd97749ce6b780b856b03b |
7dabf87617d646a9ec3e135b5f0e5edae50cd3b9 |
681b15a43925e02d7f4f0c9e554e8d73e230931ce6634f49dd5b204afd03d20c |
|
dc17bccb3790a369c858cf3e3f5c7d84 |
a31642046471ec138bb66271e365a01569ff8d7f |
73a46441a7135296d1070f5905a5cb6453ea8511a99a3b9c76060069aa7abcef |
|
f0f4bc53d852e0647dd7efd6d03386e2 |
a88f34c0b3a6df683bb89058f8e7a7d534698069 |
79a5ac15d0de66df3dd00a4148aa76dc183ebf47553fbcc5355f4902dc981267 |
|
6969fe53d3de5128ccdcdb65cfd5e017 |
aa6a9c25aff0e773d4189480171afcf7d0f69ad9 |
84b046a4dbfcd9d4b2d62b4bc8faaf4c6395696f1e688f464bc9e0b760885263 |
|
3850133c5dd8e08f5114aad927ee9954 |
c43b0006b3f7cd88d31aded8579830168a44ba79 |
8634988a90e69d8e657f72cf5f599176be5854448e0544abc42eb49b0c245f0c |
|
52c20ff058199f7ce2f8c5b181495ee9 |
cb2d18fb91f0cd88e82cb36b614cfedf3e4ae49b |
8bf0d693033a761843ae20c7e118c05f851230cb95058f836ffe2b51770f788a |
|
b705e65e02f4afbd5cc13db24f4f6d02 |
cbe82e23f8920512b1cf56f3b5b0bca61ec137b9 |
9170503615e4d2cf1d67f0935ded3ce36a984247ae7f9ab406d81ebe1daf3604 |
|
a9d6f2114865a516432837a56e085d4c |
ebe6068e2161fe359a63007f9febea00399d7ef3 |
974c221c75c35d03dd2158d1d1a0a72a7ae85a6f7c1c729977f3676f946758ee |
|
65fa3c97e450813bb51c05f27cc7f06f |
f52e18b7c8417c7573125c0047adb32d8d813529 |
a83f218d9dbb05c1808a71c75f3535551b67d41da6bb027ac0972597a1fc49fe |
|
db47c34160e6ca4fd01acca5e54806a2 |
653b2b2577770bfbb3f5e96c22d3f15bcfa84841 |
a8abffa5d7259a94951d96ad3d60e8910927b5d0697f8edece2e295154e00832 |
|
1a48334c4d6c3a83e3f7ab7eb7a3bdba |
9b8e47639f8f63ce0e2aff710c8d68b92a49d35d |
b9bb43b725a454e826ab64fdd6256af809c60119dab2876d081b3721d226c672 |
|
f444fc116f12e0a22a2db919dd1596f7 |
b746c91e014205db94f775bb6db480387c9ebc20 |
bb3f433799c30a8aad5257abc2df479ecad058f6099fd89fb8e7c278dfe3be45 |
|
a0b13d4caa1eea614816967aa3de3e00 |
19138d3c197ee1e59756d1f4fc3fd66809f44c1b |
bd299b5e3d7645b10286410f98f6ec79d803ce2b977c61e49f2dc26285823c99 |
|
47e54fd731dc969b31a7feb7007da988 |
39300863bcaad71e5d4efc9a1cae118440aa778f |
c33723a6c0ece4f790396f5fd5133cf384143736e6acd06e1d7642c04757bbae |
|
91518618c019c2bf7757aff11d01b7fe |
02e6ff95949fdf341daee846820d40289ab65985 |
c3e7089e47e5c9fc896214bc44d35608854cd5fa70ae5c19aadb0748c6b353d6 |
|
1a851934a3183d452f462fe74019100e |
6ac2d77631f775797cd0029e199a5dfe83f47b4c |
d8343068669d8fbb52b0af87bd3d4f3579d76192d021b37b6fd236b0973e4a5d |
|
3bd4d83a6dbb2c0b8b9c05edfb282567 |
769a45c84d68c650ccc5ab35d3577992379afd4d |
dc409e9fa8b8c031c347d9c36f5732ea03e246c29d73e3425e4e8aaa1da6ff7c |
|
91769e1a0d19144cd961eaa7fb787a52 |
ffa8902ae020e85471722af45815dba56c0e9208 |
dcfa26a38a5af8a072104854fba1b7c0aa9ec99875d35dbd623c12932df44969 |
|
8c037a4c447440c1cfd8b7a761c88670 |
863705828ced74f2172df4d5014f6d546acb9bde |
e4a6be2fb70603f1545641240680b44e21b5601e8016c0d144711423eef9778e |
|
e746c4d475a77a6d4a52786eed7e0060 |
df79bd0bfefc1db3289db14d9fbf61a5f730cca2 |
e848a0f1900e2f0be9ed1ea8e947ae3bae14e78f3ff81c02d8e5a54353cdbac8 |
|
196ed491c38916902f2cdac287d15e6b |
098e753f0491e1eac63369e9a2662320a93420cb |
e9b9cdb713bfea40e13acffbe90faa536df206675819035835ce9218365cd118 |
|
a09639208ce794ec515a1f04346fc5ef |
ae50ed9473db0810d521ca75b2d5358abbe9ed76 |
e9cd7c4db074c8e7c6b488a724be1cd05c8536dae28674ce3aa48ebb258e3c31 |
|
a160f19baa5e721a8b5c821fd6b91f3f |
|
f5adef8c202e62125be49f748ed3b30b34e0fb2c9539c805dd96a75a26c7ddc4 |
|
9d514fb7eb3fb84a7a6ffcd24cca7e3c |
|
f76b456cf2af1382325c704bf70b5168d28d30da0f3d0a5207901277e01db395 |
|
571a689a6351617f57e1580f75800da6 |
|
fed1c094280d1361e8a9aafdb4c1b3e63e0f2e5bb549d5d737d0a33f2b63b4b8 |
|
a83cc86952a8b4d4a17d5dd413319624 |
|
27d90611f005db3a25a4211cf8f69fb46097c6c374905d7207b30e87d296e1b3 |
|
9f7997bebbb768dcb6a23075abd422f2 |
|
8fdee53152ec985ffeeeda3d7a85852eb5c9902d2d480449421b4939b1904aad |
|
68c7c2fd3fab8401c20128f758dafae9 |
|
821efc0823b05001cb682190a5966005b15e16e09ad9bf3546437146c87e454b |
|
5919b7b8a2152478400fc095a63e496b |
|
e3bd2252bd0656210a36b185313d66acfaac03f6b4de68c66448efa9112898a7 |
|
2af70363defd468c3a93d7166c857e7f |
|
ec45ebd938e363e36cacb42e968a960fbe4e21ced511f0ea2c0790b743ff3c67 |
|
ac8d1b5e18a9b67ba3ee61c14c7d3946 |
|
25117dcb2d852df15fe44c5757147e7038f289e6156b0f6ab86d02c0e97328cb |
|
62e3dd6bd77d349c920ce998f2acfc0d |
|
4775dfb24f85f5d776f538018a98cc6a9853a1840f5c00b7d0c54695f03a11d9 |
|
406bafb46dafcbb6a563cd8fd737839e |
|
ffd09a5c27938d1f7424ed66d1474cfeb3df72daabdf10e09f161ed1ffd21271 |
|
ff8023982549e43351eeafe68bca91e2 |
|
57f0888ec2f3eb3643c91761e5ca62fd9cad22ea3f029826c935e07ff3aa8344 |
|
f421f857699068ed15d1044ad392733c |
|
d47a984c7a6b3057487ce50a71b2b59de315892ebd1d990a46722ae8d821268b |
|
b438eaf01ca16848e200b4003bb79868 |
|
f048b360433bef2170008965dd69d5fbd41f3c9b831903e313172f35cf9a7039 |
|
f48174b50d5ea87c31fcd4a32b997740 |
|
c7d5cce1723f381f9c9975d3abc6c684afd399c7271d01ad281b2641c430ec3b |
|
64a051fe115d088ef92a08dcb98a918c |
|
2090bdae4d49cc0a20526b8d57c5928500eadab334764b89810e0b08f907308a |
|
f4bc1ca7a3834a28258473f1869b2ca4 |
|
4ac7751af246df33e8d417b1eb4c499da9dc667b49188aa5b7716f6f95ff867d |
|
7b87c46bf073e7ce7cddee2a18d24af7 |
|
2883d9534021c076a27319496686408feda6fdc96e671767a856d3b1192c6d0b |
|
1c1106effbf6c2c156575d381c0d691f |
|
|
|
eb9ba2e5d44e9e839c29a2ad8600aef0 |
|
|
|
bd55d5ec3637c8b8a4bff86c4894c53e |
|
|
|
ae999dfdb6732d44bed45efb33ff8e0a |
|
|
|
e0076210a13e0ba4873ad43690e5aed6 |
|
|
|
dfe1bb50401d1155fcfa91cfea984cf0 |
|
|
|
0fc739521366cfaae8fcd7effce0bc24 |
|
|
|
97865767b37cf51a028fcb975907024d |
|
|
|
69e11b742aa2a17fa1c3774d03095601 |
|
|
|
35e8fd89f2ac5a0305339863a7a49b01 |
|
|
|
dbdc7bc6e8ec38a62ff145c18b76eaad |
|
|
|
4fd20c463fb264ae707ade6e5ec17082 |
|
|
|
6e36d111c33d9f3fbd3e5cc3b8b01ac1 |
|
|
|
411dc82655fb22c5d2949cf82d7cfabe |
|
|
|
69128eb14d024af1c7853eec24b65ab1 |
|
|
|
f3df615ebc00fb5b28470da65d32dde2 |
|
|
|
148e5cc4ccb5e41a763c47b20f053a39 |
|
|
|
b75f69446c568cd3290a8042515e6ed5 |
|
|
|
e1bbc8d041cebc4bcae85ea431b4f83b |
|
|
|
6bddac15809ba55193252c4da3849933 |
|
|
|
2516298381cb134e8ee2ba1060ea4c08 |
|
|
|
1b6e313b0d885c1257bba6b2ce5a165d |
|
|
|
b46f8f246c0d6101e92036ffa2badff9 |
|
|
|
5daaca646d8d7da6705d59d030cb8434 |
|
|
|
788723fa52b1416e9b2058cb4b3b2ada |
|
|
|
92589980ddc84b57c647007535577198 |
|
|
|
d7784bdd49c73036e59b5265aa061c0d |
|
|
|
86fcdcf0943ef200e22b2ea2d1355887 |
|
|
|
a543ac7cae12eeb39cc9c74eea0e5d85 |
|
|
|
02ade54a22573144f9a737f0d34aea5b |
|
|
|
56500d91ea6803b6793bfc09bfb0dbbb |
|
|
|
fe9ca961a482d2b66f44b6815c8e2b15 |
|
|
|
cb838d71168fff0acf1ae103cd93e3cf |
|
|
|
ec33cbe563957d5b514ab9039c0c3439 |
|
|
|
add66922e9a184ca3797653362153da1 |
|
|
|
b3657f2245bb5fe625759ac928877627 |
|
|
|
3a1b5c3754103eecb47828e59d3c6dd0 |
|
|
|
4805c42a3ae4d5e4e16bc7968ad0b71b |
|
|
|
9bd05a058deafb3c624be63507c8ca23 |
|
|
|
0ebcb4e87ddb179554f908e07abff663 |
|
|
|
e9d0048d751a89e68a05bf5973e125fb |
|
|
|
8483249f0b4d19eef7f01d815c2181e2 |
|
|
|
3404e568bd578d43de77360beac20b9f |
|
|
|
6c4d3768b9394868f505eaeb7439bf41 |
|
|
|
8d918adf85d26759588c06325ce52986 |
|
|
|
e7577c33f00c3c3d9150bcd9cfae8f68 |
|
|
|
95dc813a1b5d38adfd1ea70e301cbca1 |
|
|
|
157a22689629ec876337f5f9409918d5 |
|
|
|
1dfe0e65f3fb60ee4e46cf8125ad67ca |
|
|
|
3437e3e59fda82cdb09eab711ba7389d |
|
|
|
450769b8ae91b551ce93c36195fd1eb4 |
|
|
|
eba5bfca73c2754fbf93ed64fa224132 |
|
|
|
6f3a658fc32b4a378716ac167ebaf5ac |
|
|
|
a768244ca664349a6d1af84a712083c0 |
|
|
|
8e0b1f8390acb832dbf3abadeb7e5fd3 |
|
|
|
1cc1534b70b8d2b99b69a721c83e586a |
|
|
|
9a85d3cdeb19c81f2d694f91c294b56f |
|
|
|
1c9c189ab4d112781f6b83fdd97ea838 |
|
|
|
713215ad1495c38dff844fb5464f1f4b |
|
|
|
89a1b16b8f54b05a621fdc995cd75a68 |
|
|
|
8e7e9332ada22fda7defe16c971d610c |
|
|
|
d74f805d0a7ace6479bc70a1249a742a |
|
|
Conclusion:
Targeted ransomware and data exfiltration attacks are rapidly becoming one of the most critical threats facing the automotive manufacturing industry. With operational continuity, intellectual property, and customer trust on the line, manufacturers must adopt a proactive and layered cybersecurity approach. Leveraging threat intelligence, early warning advisories, continuous monitoring, and robust attack surface management can help detect risks before they escalate. By combining these measures with strong incident response planning and resilient backup strategies, the industry can enhance its defenses and maintain resilience against increasingly sophisticated cyber adversaries.
At CyberXTron, we specialize in Autonomous Digital Risk Protection and AI-driven Threat Intelligence tailored for protection against hacktivist threats and targeted cyber-attacks.
Click here to Book a free consultation with our expert team!!!