
Ransomware Report : March 2026
March 2026 Ransomware Report
Executive Summary
In March 2026, ransomware activity recorded approximately 832 victims worldwide, marking a 6.1% increase from February and continuing an upward trend in global ransomware incidents. This surge reinforces an accelerating trend that has seen month-over-month growth since Q4 2025. The United States continued to bear the greatest burden, accounting for 333 victims and representing over a third of all globally attributed incidents. Manufacturing retained its position as the most heavily targeted confirmed sector (96 victims), followed by Technology (87 victims) and Healthcare (51 victims). A substantial proportion of incidents — 321 victims — remained without confirmed sector attribution, reflecting persistent visibility gaps in underground reporting channels.
Introduction
This report provides an in-depth assessment of ransomware victim distribution by sector and geography during March 2026, including a comparative analysis with February 2026 to identify shifts in threat actor activity, sector targeting patterns, geographic impact, and overall victim volume. The findings are intended to support cybersecurity leaders and response teams in strengthening defensive posture and operational preparedness.
Key Points
-
A total of approximately 834 ransomware victims were recorded globally in March 2026.
-
Ransomware activity increased by approximately 6.1% from February to March 2026, continuing a multi-month upward trajectory.
-
The United States accounted for 333 victims, remaining the dominant target geography and representing approximately 35% of globally attributed incidents.
-
"Not Found" sector classification accounted for 321 victims, indicating incomplete attribution in underground reporting channels.
-
Among confirmed sectors, Manufacturing (96 victims), Technology (87 victims), and Healthcare (51 victims) were the most targeted.
-
Financial Services (41 victims) and Business Services (38 victims) reflected continued targeting of compliance-heavy and operationally sensitive environments.
-
Canada (20 victims), the United Kingdom (33 victims), and Germany (29 victims) were among the most impacted countries outside the United States.
-
The broader ransomware trend shows that the baseline has shifted upward significantly — the second half of 2025 averaged 732 claims per month compared to 521 in the first half, a 40% increase — and the March 2026 data confirms that elevated levels have not receded.
Ransomware Activity — March 2026
Ransomware activity in March 2026 demonstrated sustained and expanding global reach, with victim counts remaining heavily concentrated in North America and Western Europe while showing notable growth in other regions.
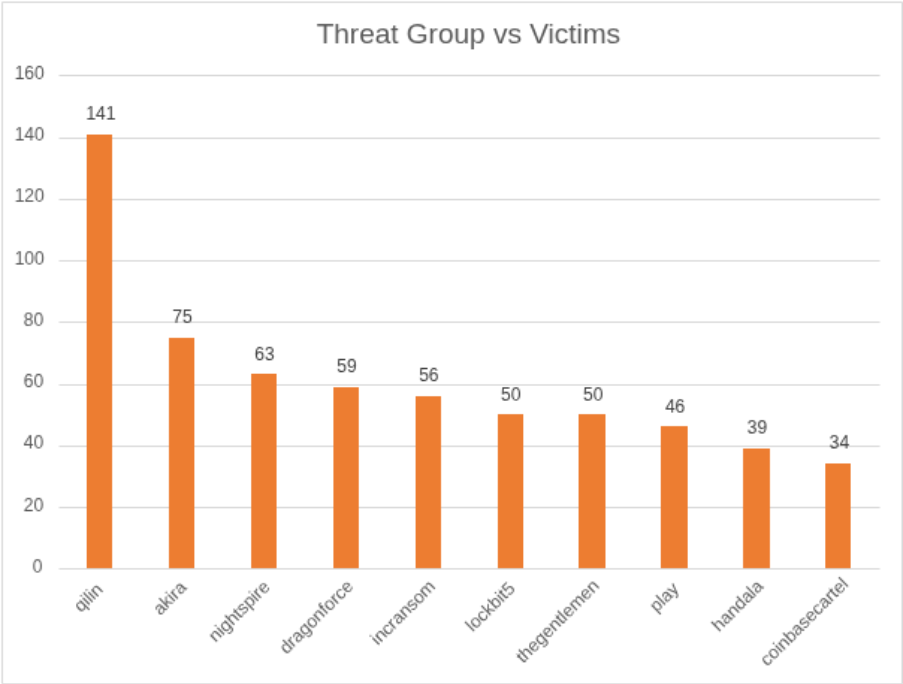
Qilin maintained its dominant position as the most active threat group with 141 recorded victims, extending its streak as the leading operator for a third consecutive month. Qilin, written in Golang and operating a double-extortion model demanding payment for both a decryptor and non-release of stolen data, has continued to expand its affiliate base and operational reach. Akira followed with 75 victims, consolidating its position as the clear second-tier operator. Akira maintained a strong second-place position, targeting retail, financial services, and professional services organizations.
Nightspire (63 victims) and Dragonforce (59 victims) demonstrated strong upward momentum, signaling aggressive affiliate scaling and expanding campaign infrastructure. Incransom (56 victims) remained operationally consistent, while LockBit5 (50 victims) and TheGentlemen (50 victims) sustained high-volume campaign activity. Play continued its steady operational tempo with 46 victims.
Several mid-tier operators contributed meaningfully to overall activity levels. Handala (39 victims) demonstrated continued presence, with a noted focus on regional and critical infrastructure targets. CoinbaseCartel (34 victims) and AiLock (24 victims) established themselves as growing mid-tier threats. On a single day in early March, AiLock led daily activity with 18 identified targets, while Play and Qilin also remained highly active.
Emerging or steadily active groups including Payload (21 victims), Genesis (17 victims), and ShinyHunters (16 victims) further diversified the ecosystem. Numerous smaller collectives, including WorldLeaks (16), Lapsus$ (10), SafePay (8), KillSec (8), Sinobi (7), Embargo (6), Everest (6), Chaos (6), and Pear (6) rounded out a densely populated threat landscape. The overall distribution continues to reflect a concentrated yet expanding ransomware environment in which a handful of high-volume operators drive the majority of incidents, supported by a broad base of mid- and lower-tier actors.
Ransomware Activity — February 2026 vs. March 2026
Ransomware activity increased from 784 victims in February 2026 to approximately 832 victims in March 2026, reflecting an approximate 6.1% month-over-month rise.
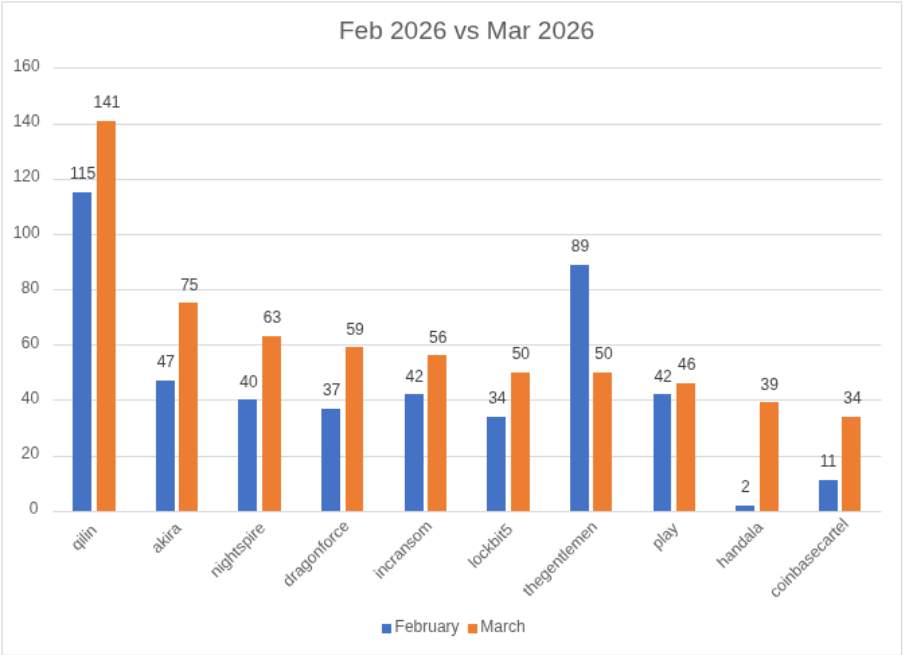
Qilin extended its lead, rising from 115 victims in February to 141 in March, reinforcing its status as the most active group for a third consecutive month. Akira demonstrated the most notable recovery among established operators, surging from 47 to 75 victims and reclaiming a strong second-place position after its February decline.
Nightspire continued its sharp upward trend, rising from 40 to 63 victims, while Dragonforce nearly doubled its February count of 37 to reach 59 victims in March, indicating aggressive affiliate expansion. Incransom grew from 42 to 56 victims, and LockBit5 maintained strong momentum from 34 to 50. TheGentlemen, which had surged to 89 victims in February, moderated to 50 in March, suggesting a partial recalibration after its February peak.
Play declined slightly from 42 to 46 victims — a marginal shift indicating continued steady pressure rather than significant campaign scaling. Clop, which had posted 79 victims in February, saw its count fall sharply to just 2 in March, reflecting a significant operational slowdown consistent with Clop's historically episodic campaign cadence. Insomnia, which emerged with 25 victims in February after no January activity, dropped to 4 victims in March — potentially reflecting a short-lived campaign burst rather than a sustained operational posture.
New entrants and emerging actors in March included Handala (39 victims), CoinbaseCartel (34 victims), and AiLock (24 victims) as notable additions to the mid-tier landscape, further diversifying an already competitive ecosystem. A mid-week spike on March 11 saw 53 attacks logged in a single 24-hour window, accounting for nearly 30% of one week's total volume — a pattern often associated with affiliates batch-uploading exfiltrated data to leak sites simultaneously.
Overall, March 2026 reflected accelerating campaign volumes, active affiliate realignments, and the continued structural resilience of the RaaS ecosystem.
Industry Impact in March 2026 — Ransomware Continues to Target Critical Sectors
In March 2026, ransomware attacks continued to concentrate on high-value and operationally essential industries, with the sectoral targeting pattern broadly consistent with February but reflecting notable shifts in volume.
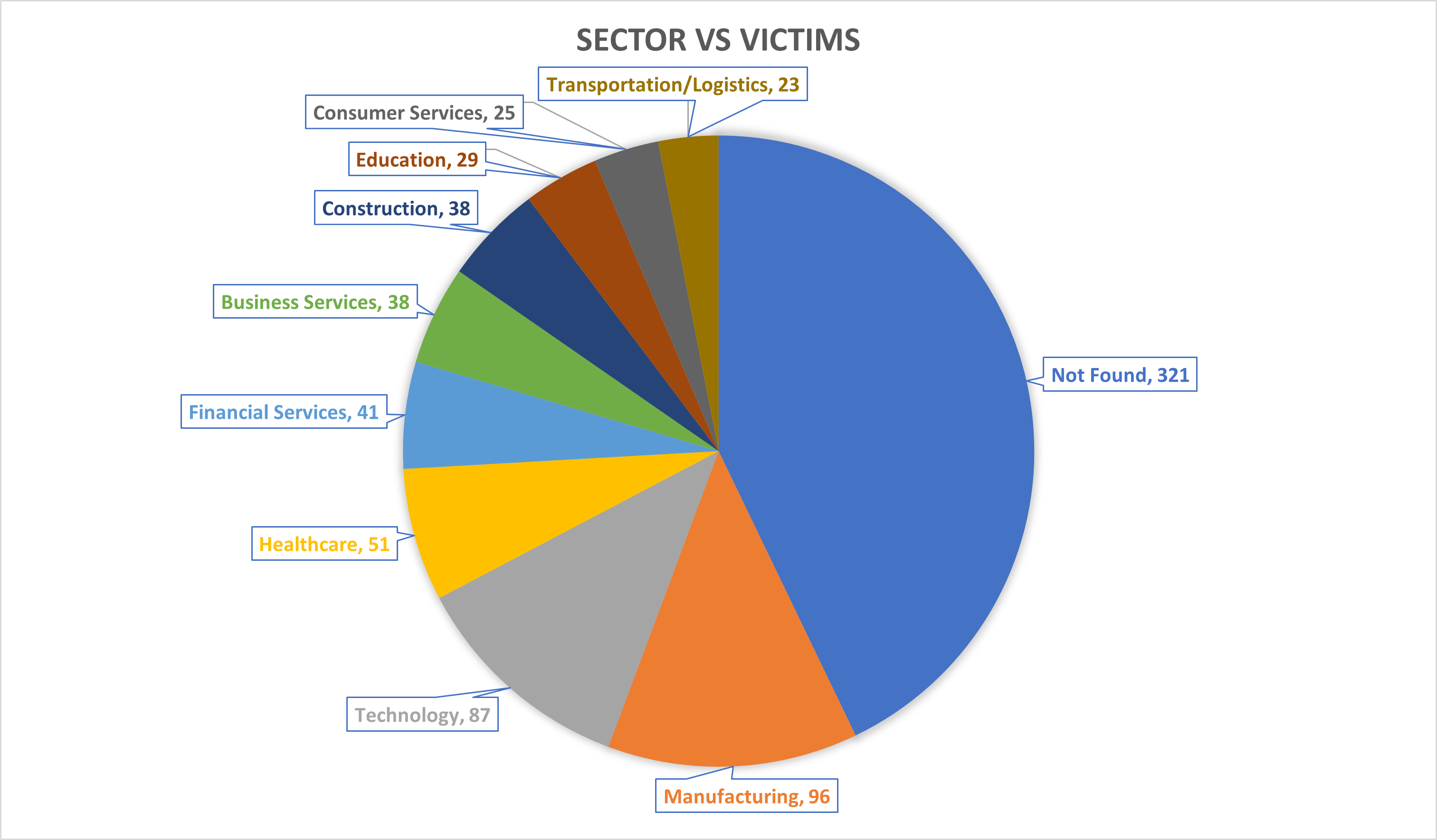
Manufacturing recorded the highest confirmed victim count at 96, displacing Technology from the top position it held in February. This likely reflects continued attacker preference for sectors where operational disruption creates acute payment pressure. Technology followed with 87 victims, remaining a primary target due to reliance on uptime, exposure of sensitive intellectual property, and supply-chain interdependencies. Healthcare recorded 51 victims, continuing its pattern as the third most targeted confirmed sector.
Financial Services (41 victims) and Business Services (38 victims) reflected sustained targeting of compliance-heavy and data-rich environments. Construction (38 victims) and Education (29 victims) remained significant targets, with Education showing notable growth relative to prior months, consistent with broader observed trends of increasing attacker attention to academic institutions. Transportation and Logistics (23 victims) and Consumer Services (25 victims) also experienced meaningful disruption.
Public Sector (22 victims) and Agriculture and Food Production (19 victims) remained consistent secondary targets. Hospitality and Tourism (14 victims), Telecommunications (6 victims), and Energy (22 victims) rounded out the confirmed sector distribution.
A substantial proportion of incidents — 321 victims — fell under "Not Found," highlighting ongoing limitations in publicly disclosed sector data from underground reporting channels. Overall, the distribution continues to reinforce attackers' preference for industries where operational disruption directly translates into increased ransom leverage. Data exfiltration has become the primary lever of extortion, with 80% of ransomware incidents in the current threat cycle involving confirmed data theft.
Geographical Distribution of Victims
The United States remained the most targeted country in March 2026 by a substantial margin, accounting for 333 victims. North America continued to represent the epicenter of ransomware activity. The United States accounted for approximately 50.8% of total global attacks, with a notable shift toward small-to-medium professional services, including law firms and architectural firms, observed during mid-month activity.
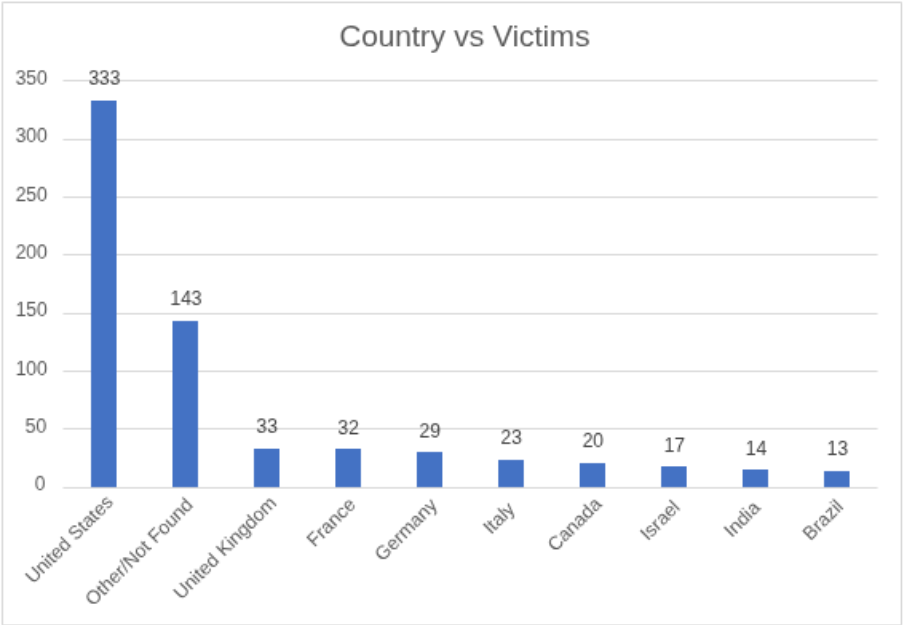
The United Kingdom recorded 33 victims, an increase from February, reflecting sustained pressure on British organizations particularly in professional services and public-facing sectors. France (32 victims) and Germany (29 victims) maintained significant exposure within Western Europe. Italy (23 victims) and Canada (20 victims) also experienced notable targeting.
In the Middle East, Israel recorded 17 victims, a higher figure than most prior reporting periods. India (14 victims) and Brazil (13 victims) led activity in Asia-Pacific and Latin America respectively. Japan (10 victims), Spain (10 victims), Taiwan (9 victims), and Australia (7 victims) maintained consistent exposure in Asia-Pacific. South Korea (7 victims) showed measurable activity, as did Switzerland (6 victims), Mexico (6 victims), China (5 victims), Belgium (5 victims), and Thailand (5 victims).
Other countries including the Czech Republic, South Africa, Turkey, Philippines, Colombia, Argentina, Malaysia, Peru, Puerto Rico, Panama, Romania, Oman, Finland, and Portugal each recorded between 2 and 5 victims. A further 143 incidents were attributed to "Other/Not Found," reflecting incomplete geographic attribution in public leak disclosures.
In total, victim organizations were identified across more than 60 countries, underscoring the continued global reach of ransomware operations. Threat actors continued to prioritize regions with advanced digital infrastructure, higher ransom payment capacity, and mature enterprise environments. Asia-Pacific has also seen a significant surge in exposure, with attacks across the region rising sharply year-over-year, particularly in East and Southeast Asia.
Major Ransomware Breaches Across Global Sectors — March 2026
During March 2026, ransomware activity produced a number of significant confirmed or claimed incidents across critical industries and regions.
Healthcare and Public Services — United States and United Kingdom Qilin was attributed to an attack on AMHC, a Maine-based mental health agency, and an attack on St Anne's Catholic School in the UK around March 22, 2026. The University of Hawaiʻi Cancer Center confirmed a ransomware attack on its epidemiology division, resulting in a data leak affecting approximately 1.2 million individuals, with exposed data including Social Security numbers, driver's license numbers, and health-related information.
Political and Government Institutions — Europe Qilin was attributed to a ransomware incident affecting the German political party Die Linke around March 26, 2026. ALP-001 compromised Jaxa.jp (Japan Aerospace Exploration Agency), underscoring persistent pressure on government and critical research entities.
Professional Services and Financial Sector — North America Notable victims during mid-March included von Weise Associates, a Chicago-based architecture firm, and Pinnacle Tax Inc., a financial consulting firm, both claimed by Qilin. Akira maintained targeting across financial services and retail organizations throughout the month.
Transportation and Critical Infrastructure — The targeting of a Class II regional railroad (Florida East Coast Railway) by ransomware operators underscored significant threats to supply chain logistics and transport security.
Emerging Threat Vectors TeamPCP compromised Telnyx's PyPI package, embedding malicious payloads via WAV steganography, subsequently launching a mass affiliate program with Vect ransomware — with AstraZeneca identified as a claimed victim. BianLian ransomware was also observed spreading via Venezuela-focused phishing campaigns using fake invoice SVG images to deliver Go-based payloads.
These incidents collectively underscore ransomware groups' continued emphasis on data exfiltration, operational disruption, and reputational pressure to maximize financial return across a broadening range of victim profiles and attack vectors.
Recommendations — March 2026 Ransomware Outlook
To mitigate the ongoing and intensifying ransomware threat, organizations should continue strengthening defensive resilience through layered controls. VPN devices accounted for 68% of remote access exploit cases in recent incident data, with nearly 70% of associated incidents linked to Akira campaigns — highlighting the critical importance of hardening or retiring vulnerable VPN and RDP pathways and reviewing patch cadences for public-facing infrastructure.
-
Deploy advanced EDR/XDR solutions and continuously monitor for indicators of compromise across endpoint and network telemetry.
-
Enforce rapid patch management for VPNs, cloud services, exposed web applications, and third-party software dependencies including package repositories.
-
Implement phishing-resistant MFA across all remote access channels and review session-token lifecycles to mitigate adversary-in-the-middle attacks.
-
Segment enterprise networks to limit lateral movement and reduce blast radius following initial compromise.
-
Maintain offline, encrypted, and regularly tested backup systems. Emerging AI-driven ransomware is evolving to autonomously map recovery points and compromise backup repositories, making immutable offline copies and behavior-based detection increasingly important.
-
Conduct regular incident response exercises and ransomware simulation drills calibrated to current threat actor TTPs.
-
Extend third-party and supply-chain risk management to software dependencies, managed service providers, and vendor ecosystems.
Conclusion
The ransomware landscape in March 2026 reflected an acceleration in both volume and diversity, with victim counts reaching their highest levels in the current reporting cycle. The United States remained disproportionately affected, while the United Kingdom, France, Germany, and Israel experienced elevated targeting within their respective regions.
Sectoral distribution confirms a persistent prioritization of Manufacturing, Technology, and Healthcare, alongside meaningful targeting of Financial Services, Construction, and increasingly, Education and Public Sector organizations. The entry and growth of mid-tier operators such as AiLock, Handala, and CoinbaseCartel signals continued ecosystem expansion, reducing reliance on any single dominant group and complicating defensive prioritization.
With 129 active groups having posted victims across 141 countries in the March 2025 to March 2026 observation window, no single law enforcement action is likely to reduce overall volume substantially — the top group accounts for only 15% of claims, meaning the ecosystem remains structurally resilient even against targeted disruption efforts.
Ransomware remains a persistent, adaptive, and strategically driven threat, continuing to evolve in geographic reach, sectoral focus, and technical sophistication. The structural resilience of the RaaS ecosystem, combined with the growing role of data exfiltration as the primary extortion lever, underscores the need for sustained investment in detection, response, and recovery capabilities.