LAMASHTU Threat Report: An Emerging Data Extortion Group Targeting Global Organizations
Executive Summary
LAMASHTU is an emerging data extortion group observed in April 2026, operating through a centralized leak platform with structured and staged data disclosures, supported by peer-to-peer (torrent-based) distribution mechanisms that expand data dissemination beyond traditional leak sites. Its activity spans Europe, North America, and Asia-Pacific, with approximately 21% of victims concentrated in France, and targets data-rich sectors led by Business Services (~29%) and Manufacturing (~22%). The group demonstrates rapid operational execution, with 14+ victims disclosed within a short timeframe, while its operations are centered on large-scale exposure of sensitive data, creating sustained risk through continued accessibility and third-party exploitation. The inclusion of explicit ransom demands alongside exposure threats reflects a dual-impact extortion model, positioning LAMASHTU as a developing threat leveraging data exposure as a primary mechanism for coercion and financial gain.
Key Insights
Structured leak platform operations with staged disclosure workflows indicate a controlled and repeatable data release model sustaining pressure
Peer-to-peer (torrent-based) distribution expands dissemination beyond the leak site, increasing long-term exposure risk
~21% of victims are concentrated in France, with activity spanning Europe, North America, and Asia-Pacific
Business Services (~29%) and Manufacturing (~22%) lead sector targeting, highlighting focus on data-rich environments
Rapid onboarding of 14+ victims with ransom demands reflects a dual-impact extortion model combining scale and coercion
This is an ongoing and developing story that CyberXtron™ will update as new information emerges from our monitoring and analysis
Threat Profile
GROUP OVERVIEW
LAMASHTU derives its name from Mesopotamian mythology, referring to a demonic entity associated with harm, disease, and predatory behavior, acting independently and inflicting damage without external control.
LAMASHTU is an emerging data extortion group observed in April 2026, initially identified as a newly listed ransomware-claim entity with a minimal public footprint. Observed leak entries indicate activity emerging in early April 2026.
The group has established a dedicated leak platform where victim disclosures are published alongside descriptions of compromised data. Its activity reflects a clear focus on acquiring, organizing, and releasing sensitive datasets, with operations centered on large-scale data exposure. The group is actively handling and distributing significant volumes of organizational data, positioning itself within the extortion ecosystem through exposure-driven operations rather than demonstrated encryption-based attacks.
Operational Characteristics
LAMASHTU operates through a centralized leak platform where victim disclosures are published in a consistent and structured manner. Each disclosure presents a narrative of compromise and highlights the nature of the exposed data, focusing on business operations, financial records, personnel information, and internal documentation.
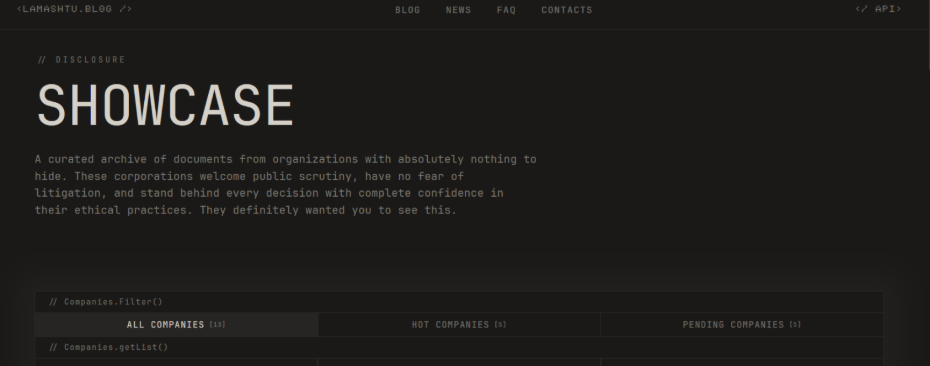
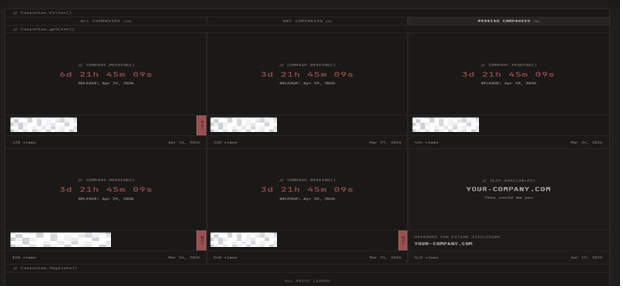

(The group’s leak platform interface displays active and pending disclosures with release timelines, reflecting a structured and continuously managed data publication process.Company identifiers have been redacted for reporting purposes)
A defining characteristic of the group is its approach to data handling and release. The group not only presents exposure narratives but also enables access to the compromised data, indicating active involvement in staging and distributing information rather than limiting activity to public claims. Observed entries include release countdowns and publication timelines, suggesting that disclosures are scheduled and actively managed as part of a continuous release cycle. The group’s data dissemination approach extends beyond its leak platform, with observed use of peer-to-peer distribution mechanisms enabling broader access to exposed datasets across external networks.
Recent disclosures further indicate the inclusion of explicit ransom demands, with affected organizations being threatened with public data release. This reflects an evolution toward a more direct extortion model, where data exposure is used as leverage to enforce compliance. The disclosures consistently emphasize downstream impact, outlining how exposed data can be leveraged by regulators, competitors, or external parties, reinforcing an extortion model built on pressure through visibility, accessibility, and long-term consequences of data exposure. Observable network activity patterns further suggest coordinated data distribution through a limited set of active nodes, indicating controlled dissemination channels rather than fully decentralized sharing.
Impact
The impact is centered on large-scale exposure of organizational data across multiple domains, including financial records, personnel information, legal documentation, operational data, and intellectual property. The depth and breadth of exposed data indicate access to core business systems and long-term organizational records. In several cases, the information includes sensitive personal data, internal communications, and system-related artifacts, increasing both regulatory and operational risk.
A critical factor is the group’s role in facilitating data distribution, where exposed information becomes accessible beyond the initial disclosure, enabling independent use by third parties and extending the impact from a single incident to persistent exposure with long-term consequences. The observed use of peer-to-peer distribution mechanisms further amplifies this impact by enabling broader and decentralized access to exposed datasets, reducing control over data propagation once released. Recent activity further indicates the inclusion of explicit ransom demands, where affected organizations are threatened with public data release. This introduces a combined exposure and coercion model, elevating the impact from passive data leakage to active extortion scenarios where organizations face both reputational damage and enforced negotiation pressure.
The resulting risk is multi-layered:
Exposure of sensitive internal operations
Regulatory implications due to personal and protected data
Competitive risk from business and intellectual property data
Sustained reputational impact driven by public availability
Increased pressure through ransom-backed data exposure
Victimology
Overview
Total Victims (Observed): 14+
Active Since: April 2026
Countries Affected: 8+
Leak Site: Active
LAMASHTU demonstrates rapid operational activity, with multiple victim disclosures occurring within a short timeframe, indicating immediate execution and a quickly established presence. Observed leak entries indicate activity emerging in early April, followed by continued expansion of its victim set, reflecting a sustained and actively evolving operational phase.
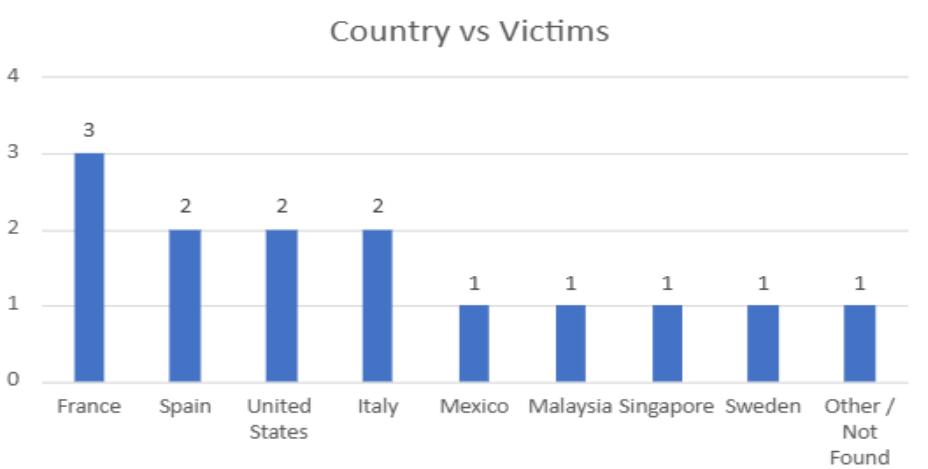
Geographical Distribution
The victim distribution reflects a multi-region presence across Europe, North America, and Asia-Pacific. The highest concentration is observed in France, followed by Spain, the United States of America, and Italy, indicating a stronger clustering across European and North American regions.
Further instances extend to Mexico, Malaysia, Singapore, and Sweden, along with a small number of cases where geographic attribution could not be confidently determined from available information. Overall, the distribution indicates a globally dispersed footprint rather than a regionally focused campaign.
Sector Targeting
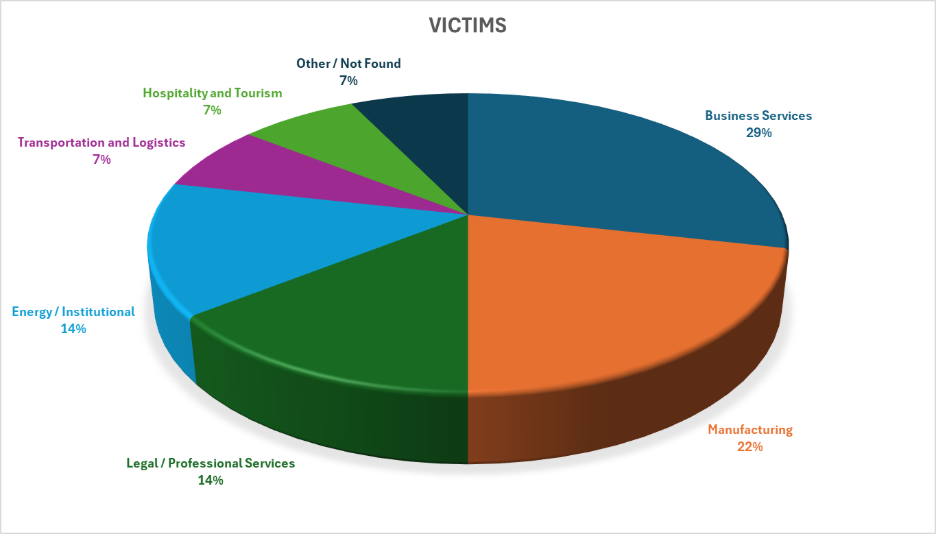
The victim set spans multiple industries, with Business Services accounting for approximately 29% of observed victims, followed by Manufacturing at around 22%. Legal / Professional Services and Energy / Institutional sectors each represent roughly 14%, indicating notable exposure within data-intensive and regulated environments. Additional sectors include Transportation and Logistics and Hospitality and Tourism, each contributing about 7%, along with a small proportion of cases where sector attribution is not clearly defined.
This distribution reflects a broad and non-specialized targeting pattern. The concentration across service-oriented sectors, combined with manufacturing and energy-related organizations, suggests a focus on entities handling large volumes of structured and sensitive data, rather than a clearly defined industry-specific targeting strategy.
MITRE ATT&CK table
The following MITRE ATT&CK mapping is based on observed behaviors
|
Tactic |
Technique ID |
Technique Name |
|
Collection |
T1005 |
Data from Local System |
|
Collection |
T1039 |
Data from Network Shared Drive |
|
Exfiltration |
T1020 |
Automated Exfiltration |
|
Exfiltration |
T1048 |
Exfiltration Over Alternative Protocol |
|
Exfiltration |
T1567 |
Exfiltration Over Web Services |
|
Command and Control |
T1090.003 |
Proxy: Multi-hop Proxy |
|
Command and Control |
T1102 |
Web Service |
|
Impact |
T1657 |
Financial Theft |
|
Impact |
T1565 |
Data Manipulation |
Indicators of Compromise (IOCs)
|
Type |
Indicator |
|
IP Address |
185[.]16[.]215[.]140 |
|
IP Address |
185[.]16[.]215[.]189 |
|
IP Address |
217[.]145[.]227[.]15 |
|
IP Address |
31[.]200[.]249[.]130 |
|
IP Address |
31[.]200[.]249[.]233 |
|
IP Address |
31[.]200[.]249[.]244 |
|
Domain (Onion) |
hxxp[://]lamashtux5j74mcm7lwwgn5yrvuwtrpxjoyendif3v3hrztjesfoyayd[.]onion |
Mitigation & Recommendations
Access & Identity Protection
Enforce multi-factor authentication (MFA) across all remote access, administrative, and critical systems
Monitor for compromised or exposed credentials and enforce periodic credential rotation
Apply least privilege principles to restrict access to sensitive and high-value data
Data Exfiltration & Exposure Prevention
Monitor outbound network traffic to identify unusual data transfers or bulk exfiltration patterns
Deploy Data Loss Prevention (DLP) controls to detect and block unauthorized data movement
Encrypt sensitive data at rest and in transit to reduce exposure risk if accessed
Monitoring & Threat Intelligence
Integrate threat intelligence feeds from CyberXtron Threatbolt into SIEM/XDR platforms for detection of extortion-related activity
Continuously monitor dark web leak from CyberXtron Darkflash and peer-to-peer channels for exposed data
Establish alerting for suspicious access, abnormal user behavior, and data access anomalies
Network Security & Segmentation
Segment networks to isolate critical systems and limit lateral movement
Restrict access between business units and sensitive data repositories
Secure internet-facing services through hardened configurations and access controls
Vulnerability & Attack Surface Management
Conduct regular vulnerability assessments from CyberXtron ShadowSpot and apply timely patching of critical systems
Minimize exposure of publicly accessible services and enforce secure configurations
Continuously validate external attack surface and remove unnecessary services
Incident Response & Data Exposure Preparedness
Develop and maintain response plans specific to data breach and extortion scenarios
Engage incident response teams and legal counsel early in the event of compromise
Prepare communication strategies for regulatory, customer, and stakeholder impact
Backup & Recovery Strategy
Maintain secure, offline, and immutable backups of critical data
Regularly test backup restoration processes to ensure operational recovery
Protect backup infrastructure from unauthorized access or modification
User Awareness & Initial Access Prevention
Conduct regular security awareness training focused on phishing and credential security
Implement phishing simulations to reduce susceptibility to social engineering
Enforce secure authentication practices across all user access points
Conclusion
LAMASHTU represents an emerging data extortion group demonstrating a structured and evolving operational model centered on the large-scale exposure and controlled distribution of organizational data. Its activity reflects a clear emphasis on visibility, accessibility, and sustained exploitation of compromised information, supported by staged disclosure workflows, peer-to-peer distribution mechanisms, and the increasing use of explicit ransom demands to enforce compliance. This indicates a transition toward a more mature extortion approach, where data exposure is not only an outcome of compromise but a primary mechanism for coercion.
The group’s activity spans multiple regions and sectors without a clearly defined targeting pattern, highlighting a focus on data-rich environments across both service-oriented and industrial domains. The scale and diversity of exposed datasets, combined with extended distribution through external channels, introduce persistent risk beyond initial compromise, including regulatory exposure, competitive impact, and long-term reputational damage. This positions LAMASHTU as a developing threat within the extortion landscape, where impact is driven by sustained data availability, broader dissemination, and the continued use of exposure as leverage for operational and financial gain.