
From Access to Encryption in Hours: TheGentlemen Ransomware Playbook Exposed
Executive Summary
TheGentlemen is an active ransomware-as-a-service (RaaS) operation observed since February 2023, with at least 223 publicly listed victims across North America, Europe, Asia, and other regions. The group employs a double-extortion strategy, combining data theft with rapid network-wide encryption and publication of stolen data on its leak site, often proceeding without prolonged negotiation phases. Instead of relying heavily on sophisticated zero-day exploits, operators frequently gain initial access through exposed services and compromised credentials, then escalate privileges, disable security controls, and deploy ransomware across the domain. Their campaigns target a wide range of sectors — particularly manufacturing, technology, and financial services — indicating opportunistic yet consistent enterprise-focused operations.
For defenders, the primary risk lies in the speed and reliability of execution. Once inside a network, TheGentlemen operators can progress from initial access to full operational disruption within a short timeframe using legitimate administrative tools and strong encryption mechanisms that limit recovery without reliable backups. Organizations should prioritize identity and access security, monitoring of Active Directory activity, network segmentation, and resilient offline backups to interrupt the attack chain before encryption is deployed. Early detection of pre-ransomware behaviors remains the most effective defensive measure, as recovery options after encryption are limited and the resulting operational disruption can be severe.
Threat Profile
Group Overview
The Gentlemen ransomware group first appeared on February 28, 2023, and remains active as of March 3rd, 2026, with 223 victims listed on their leak site. The group employs a double-extortion model, encrypting victim data while simultaneously threatening to leak stolen information if ransom demands are not met. Despite the name, the group operates with aggressive tactics and limited negotiation, often prioritizing rapid victim publication on its leak site to increase pressure on affected organizations.
TheGentlemen operates in a ransomware-as-a-service (RaaS)–style model, where core developers provide ransomware tooling and infrastructure to affiliates who conduct intrusion and deployment activities. The group maintains a dark-web leak site where it publishes victim details and exfiltrated data to enforce its dual-extortion strategy, regularly updating the platform with newly compromised organizations. The scale of activity, consistent leak-site updates, and diverse targeting patterns suggest a structured operational model supported by multiple operators or affiliates.
Operational Characteristics
The group runs a Ransomware-as-a-Service (RaaS) model with cross-platform payloads (Windows, Linux, ESXi) written in Go for stealth and compilation ease. They emphasize speed, using automated persistence, EDR evasion, and domain-wide deployment via GPO or privileged accounts. Attacks follow a structured lifecycle: initial access via exposed services, reconnaissance, security disablement, exfiltration, and encryption with XChaCha20/Curve25519.
Victimology
Geographical Distribution
TheGentlemen’s activity demonstrates a clear acceleration in operational tempo. In 2025 alone, the group recorded 81 victims, while in 2026 as of March 3rd, they have already listed 142 victims on their leak site. Surpassing the previous year’s total in less than two months highlights a significant increase in campaign velocity and affiliate activity. This rapid growth suggests expanding operational capacity, improved deployment efficiency, or increased affiliate onboarding, reinforcing the assessment that TheGentlemen is scaling aggressively rather than plateauing.
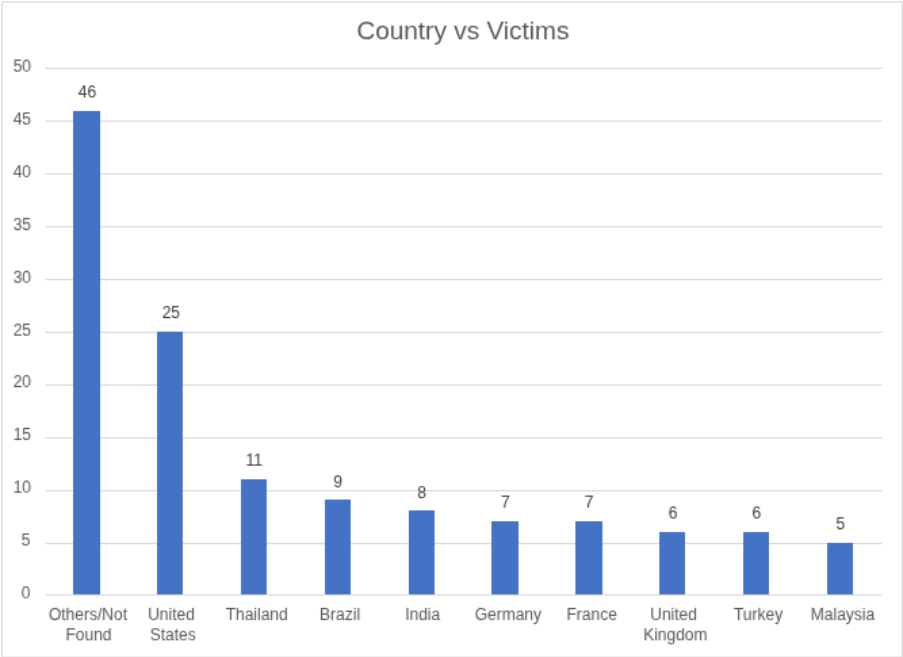
The Gentlemen ransomware group has a total of 223 victims, with 46 incidents lacking country attribution. Among identified locations, the United States recorded the highest number of victims with 25 cases, followed by Thailand (11) and Brazil (9). India reported 8 victims, while France and Germany each recorded 7 incidents. The United Kingdom and Turkey accounted for 6 victims each, and Malaysia, Indonesia, Spain, and Italy reported 5 cases each, reflecting consistent targeting across multiple regions. Additional activity was observed across Latin America, the Middle East, and the Asia-Pacific region, including countries such as Mexico, Colombia, Viet Nam, and the United Arab Emirates. Overall, the distribution indicates a globally dispersed victimology spanning North America, Europe, Asia, and other regions, rather than concentration within a single geographic area, highlighting the group’s broad opportunistic targeting strategy.
Sector Targeting
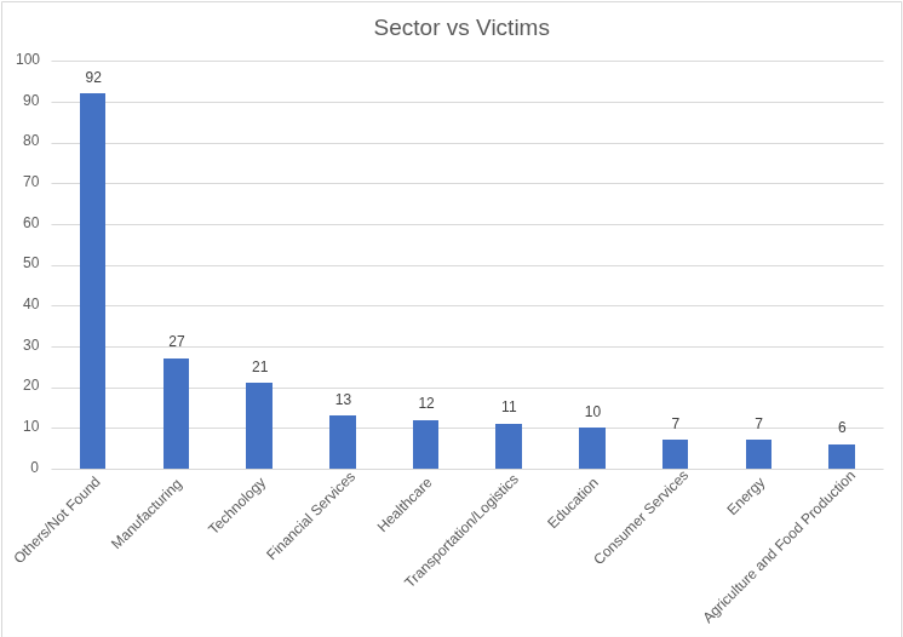
Among identified industries, the Manufacturing sector was the most affected with 27 victims, followed by Technology (21). Financial Services recorded 13 victims, while Healthcare accounted for 12 incidents and Transportation/Logistics reported 11 cases, indicating continued exposure of critical and operational infrastructure. The Education sector recorded 10 victims, while Consumer Services and Energy each accounted for 7 cases. The Public Sector experienced 6 incidents, demonstrating that government-related entities were also targeted. Additional activity was observed in sectors such as Agriculture and Food Production (6), Construction (4), and Hospitality and Tourism (3), reflecting broad sector coverage. A significant portion of incidents — 92 victims — lacked sector attribution, suggesting either limited disclosure by victims or incomplete intelligence visibility. Overall, the distribution indicates opportunistic targeting across multiple industries rather than concentration in a single dominant vertical.
Technical analysis
Initial access and foothold
Current reporting indicates two primary initial access vectors:
-
Exploitation of public‑facing infrastructure, notably Fortinet FortiGate devices, consistent with MITRE ATT&CK T1190 (Exploit Public‑Facing Application).
-
Use of compromised or stolen domain and privileged accounts (T1078.002 – Valid Accounts: Domain Accounts), often sourced from infostealer logs or prior compromise.
Once access is obtained, operators typically run Nmap and other tools for network service discovery and asset mapping, including Advanced IP Scanner, before pivoting to domain reconnaissance. They rapidly enumerate domain users, groups (including “Domain Admins” and VMware‑related groups), and domain trusts using batch scripts and PowerShell to plan privilege escalation and lateral movement.
Privilege escalation, defense evasion, and persistence
TheGentlemen places heavy emphasis on defense evasion and privilege escalation:
-
A vulnerable signed driver (often referenced as ThrottleBlood.sys) is deployed and executed by a loader such as All.exe or its variants, enabling the termination of protected security processes and bypassing kernel‑level protections.
-
Custom “kill‑AV” tools and drivers are used to systematically stop EDR/AV services, combined with registry modifications weakening authentication and RDP security settings.
-
Tools like PowerRun.exe are used to run processes with elevated privileges and to hijack execution flows, while Allpatch2.exe variants support tailored evasion of specific security controls.
Persistence is achieved via:
-
Registry Run keys and startup folder entries (T1547.001) to restart tooling and payloads.
-
Deployment of AnyDesk and similar remote‑access software (T1219) configured for long‑term remote management, often with new local or domain accounts created for operational use.
Lateral movement, exfiltration, and encryption
Lateral movement is largely based on:
-
Windows Management Instrumentation (WMI) and PowerShell remoting to push tools and ransomware across hosts, exploiting existing administrative shares and network‑shared drives.
-
Remote Desktop Protocol (RDP), SMB/Admin shares (PSExec), and, in some cases, SSH via PuTTY to move between servers, including virtualization hosts and critical infrastructure nodes.
Data theft and impact stages typically follow this chain:
-
Data staging in local directories such as C:\ProgramData\data and on network shares (T1074.001, T1039).
-
Exfiltration via encrypted channels, often using WinSCP or WebDAV over HTTPS, categorized as T1048.001 (Exfiltration over Symmetric Encrypted Non‑C2 Protocol) and T1071.001 (Web protocols).
-
Final deployment of ransomware via the Netlogon share using domain admin privileges, enabling rapid domain‑wide encryption (T1486) and stopping services that aid recovery and investigation (T1489).
Cryptographically, TheGentlemen uses strong modern primitives: XChaCha20 for file encryption and Curve25519 for key exchange, reinforcing that recovery without keys is not feasible in practice. The malware incorporates self‑restart and run‑on‑boot capabilities to ensure that even after partial remediation attempts, encryption and extortion workflows can continue.
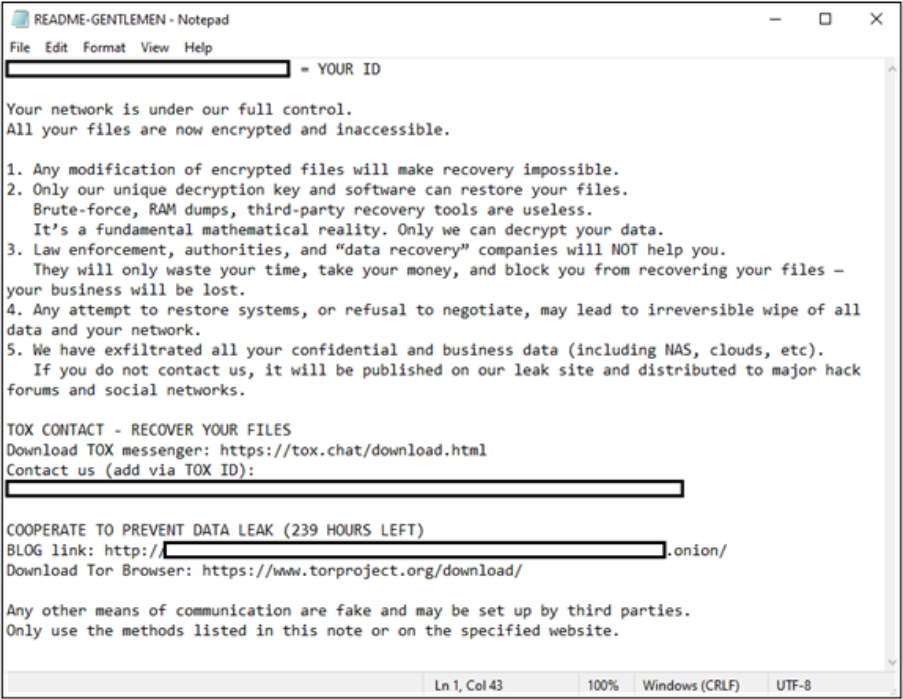
Ransomnote:
File Name: README-GENTLEMEN.txt
MITRE ATT&CK TTPs
|
Tactic |
Technique ID |
Technique Name |
|
Initial Access |
T1190 |
Exploit Public-Facing Application |
|
T1078 |
Valid Accounts |
|
|
T1078.002 |
Valid Accounts: Domain Accounts |
|
|
Execution
|
T1059 |
Command and Scripting Interpreter |
|
T1059.001 |
Command and Scripting Interpreter: PowerShell |
|
|
T1059.003 |
Command and Scripting Interpreter: Windows Command Shell |
|
|
Persistence |
T1547 |
Boot or Logon Autostart Execution |
|
T1136 |
Create Account |
|
|
Privilege Escalation |
T1068 |
Exploitation for Privilege Escalation |
|
Defense Evasion
|
T1562 |
Impair Defenses |
|
T1112 |
Modify Registry |
|
|
T1027 |
Obfuscated Files or Information |
|
|
T1484.001 |
Domain Policy Modification: Group Policy Modification |
|
|
Discovery |
T1046 |
Network Service Discovery |
|
T1087 |
Account Discovery |
|
|
T1087.002 |
Account Discovery: Domain Account |
|
|
T1482 |
Domain Trust Discovery |
|
|
Lateral Movement |
T1021 |
Remote Services |
|
T1021.001 |
Remote Services: Remote Desktop Protocol |
|
|
T1021.002 |
Remote Services: SMB/Windows Admin Shares |
|
|
T1021.004 |
Remote Services: SSH |
|
|
Collection & Exfiltration
|
T1074 |
Data Staged |
|
T1074.001 |
Data Staged: Local Data Staging |
|
|
T1039 |
Data from Network Shared Drive |
|
|
T1048 |
Exfiltration Over Alternative Protocol |
|
|
T1048.001 |
Exfiltration Over Alternative Protocol: Unencrypted/Obfuscated Non-C2 Protocol |
|
|
Command & Control
|
T1071 |
Application Layer Protocol |
|
T1071.001 |
Application Layer Protocol: Web Protocols |
|
|
T1219 |
Remote Access Software |
|
|
Impact |
T1486 |
Data Encrypted for Impact |
|
T1489 |
Service Stop |
|
|
T1552 |
Unsecured Credentials |
Indicators of Compromise (IOCs)
-
4c82fbafef9bab484a2fbe23e4ec8aac06e8e296d6c9e496f4a589f97fd4ab71
-
7a311b584497e8133cd85950fec6132904dd5b02388a9feed3f5e057fb891d09
-
7a311b584497e8133cd85950fec6132904dd5b02388a9feed3f5e057fb891d09
-
3ab9575225e00a83a4ac2b534da5a710bdcf6eb72884944c437b5fbe5c5c9235
-
51b9f246d6da85631131fcd1fabf0a67937d4bdde33625a44f7ee6a3a7baebd2
Mitigations & Recommendations
1. Identity & Access Security
-
Enforce multi-factor authentication (MFA) for all administrative and remote access accounts.
-
Conduct regular Active Directory audits and monitor for privilege escalation or abnormal authentication activity.
2. Network Hardening & Attack Surface Reduction
-
Secure internet-facing services and remove unnecessary external access to reduce exposure.
-
Implement network segmentation and restrict use of remote services such as RDP and SMB.
3. Endpoint Protection & Monitoring
-
Deploy EDR/XDR solutions capable of detecting defense evasion, driver abuse, and suspicious tool execution.
-
Restrict execution from user-writable directories and monitor for pre-ransomware behavioral activity.
4. Group Policy & Administrative Controls
-
Limit Group Policy modification rights to trusted administrators only.
-
Enable logging and alerting for GPO, registry, and domain configuration changes.
5. Data Protection & Backup Strategy
-
Maintain offline, immutable backups and regularly test restoration procedures.
-
Implement encryption and data loss prevention (DLP) to detect unauthorized data staging or transfers.
6. Patch & Vulnerability Management
-
Keep operating systems, drivers, and third-party applications fully patched.
-
Prioritize remediation of vulnerabilities in public-facing applications.
7. Threat Detection & Intelligence
-
Integrate threat intelligence indicators into SIEM and monitoring platforms.
-
Hunt for affiliate pre-deployment ransomware activity and abnormal outbound traffic.
8. Security Awareness & Organizational Preparedness
-
Conduct regular phishing and credential-theft awareness training for users.
-
Maintain and rehearse ransomware-specific incident response procedures.
Conclusion
The Gentlemen pose an evolving, high-velocity threat with 223 victims since 2023, targeting diverse sectors globally via sophisticated, adaptive tactics. Immediate adoption of layered defenses can mitigate risks, but vigilance against their evasion techniques remains essential for resilience
Overall, TheGentlemen should be considered a persistent enterprise ransomware threat rather than a short-lived campaign. Organizations are most at risk when identity infrastructure, external services, and endpoint protections are weakly monitored or poorly segmented. Effective defense therefore depends less on any single control and more on layered security — particularly identity protection, continuous monitoring, and resilient backup strategies. Proactive detection of pre-ransomware behaviors remains the most reliable opportunity to disrupt the intrusion lifecycle before irreversible impact occurs.