Dissecting Scattered Spider: SaaS Token Abuse, RMM Persistence, and Insider Access
Executive summary
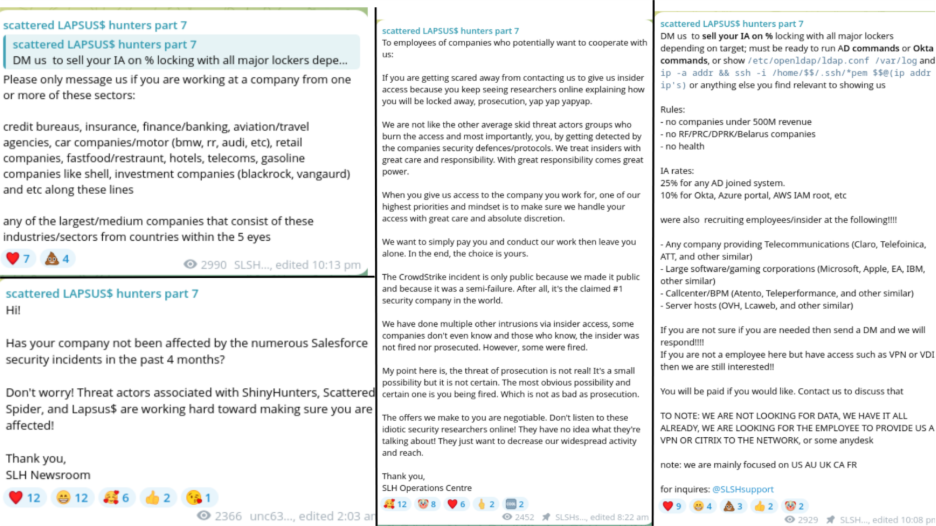
Scattered Spider (publicly tracked as UNC3944 and now operating in a broader criminal ecosystem often called Scattered LAPSUS$ Hunters - SLSH) has shifted in 2024-2025 from SIM-swap/MFA-fatigue operations into an identity-first, SaaS-supply-chain and insider-enabled extortion model. Recent activities (late 2025) include abuse of third-party SaaS integrations (Gainsight/Salesforce ecosystem), public extortion/leak theater, active recruitment and brokering of insider access, and the marketing/rollout of new RaaS families (e.g., ShinySp1d3r). About 70% of the group’s targets belong to technology, finance, and retail trade sectors and a recent increasing focus on Aviation / Airlines and Insurance. The November 2025 CrowdStrike episode appears to have involved an insider who shared screenshots externally (CrowdStrike terminated the employee); actors publicly tried to spin and exploit the publicity for recruitment. Salesforce/Gainsight “unusual activity” and token revocations in Nov 2025 underscore how SLSH-style actors now target SaaS integration tokens and third-party access to achieve mass exposures.
Profile
- Names / aliases: Scattered Spider, UNC3944, Octo Tempest, Roasted 0ktapus, and, when allied with LAPSUS$ / ShinyHunters, “Scattered LAPSUS$ Hunters” (SLSH). Vendor CTI sometimes groups overlapping activity under related case names (e.g., MITRE group G1015 / UNC3944).
- Organizational model: semi-decentralized criminal ecosystem — core operators + large orbit of affiliates, data buyers, and casual community members (“The Com” style). The group operates a public Telegram ecosystem (announcement channel + multiple open chats) used for recruitment, branding, leak publishing and coordination. Your Telegram exports capture pinned SLSH recruitment posts, insider offers, and operational messaging.
- Primary goals / monetization: purchase/broker insider access, exfiltrate SaaS/CRM data (high value), run double-extortion (data leak + ransomware), sell stolen databases to buyers, and sell RaaS/affiliate services.
Technical details
Primary attack vectors
-
Insider access procurement (human-enabled access): Operators actively buy or broker direct remote access from employees and contractors. Ads in the Telegram announcement channel specify exact proof items required before payment (for example: output of whoami/set/net user commands, a screenshot of an Okta/SSO admin panel, or an AD domain-joined machine showing domain membership). Prices are tiered by capability, the channel lists higher pay for AD-joined workstations and full cloud/identity admin access (Okta/Azure/AWS). Purchases are treated like transactionable assets: the buyer verifies the environment via screenshots or short live sessions, negotiates a payment method, and then uses the acquired VPN/VDI/RDP/AnyDesk credentials to operate from inside the target network.
-
OAuth / third-party integration & token abuse (SaaS supply-chain attacks): Rather than relying solely on stolen usernames/passwords, the group targets third-party SaaS apps and integrations that hold OAuth client secrets or refresh tokens. Once an integration (for example, a customer-success product with broad Salesforce privileges) is compromised, long-lived tokens or API keys are harvested and reused to query multiple downstream customer orgs. This approach allows mass data extraction with no endpoint foothold: attackers perform API exports or run ad-hoc queries through legitimate provider APIs, then exfiltrate data centrally. Defenders see this as a supply-chain weakness because a single compromised integration can expose many tenant environments.
-
Social engineering & push-bombing (MFA fatigue), help-desk impersonation: The actor set uses aggressive human-targeted techniques to defeat modern authentication. Push-bombing (flooding a target with approval requests until they accept) is combined with vishing (voice impersonation of IT/help-desk) and tailored phishing pages that mimic corporate SSO flows (Okta, Microsoft Entra, Salesforce). These phishing flows frequently use reverse-proxy tooling to transparently capture SSO tokens or session cookies. Operators script social approaches, pretexting to establish urgency or fear, to increase the chance a user will approve a push or disclose a one-time code.
-
RMM / Remote-Access tooling abuse & hypervisor attacks: Once inside, attackers commonly abuse legitimate remote-management tools (AnyDesk, TeamViewer, ScreenConnect) to maintain interactive access and to move laterally. The group also targets virtualization infrastructure: compromising vSphere/ESXi hosts or management consoles enables them to access VM disk images or backup repositories, which they may encrypt with ESXi-focused ransomware or use to extract corporate backups. Chat artifacts show explicit requests for ScreenConnect configurations and discussions about bypassing AV/EDR for such tools, indicating a preference for operability over bespoke malware.
Methods
-
Human proofing of insider access: SLSH requires AD/Okta proofs before purchase and the channel provides OPSEC guidance to insiders (how to avoid logging anomalies or use jump boxes), which normalizes these trade procedures and increases the chances that an insider sale leads to persistent, usable access.
-
Token reuse and mass-exfiltration: After harvesting OAuth tokens or refresh tokens, attackers iterate across APIs and tenant endpoints using legitimate API calls (e.g., Salesforce REST/Bulk APIs) to perform wide data pulls. They often automate the process: a single stolen refresh token can be used to request new access tokens and then enumerate connected orgs or export reports. Because these actions are carried out through legitimate service endpoints, they can blend into normal API traffic unless defenders monitor for anomalous client-IDs, unusual data export volumes, or token refreshes from unexpected IP ranges.
-
MFA fatigue & SSO capture workflows: The group chains together social engineering and technical tooling: a push attack to bypass MFA, followed by a reverse proxy to capture SSO cookies when the victim interacts with a spoofed login page. Alternatively, vishing convinces a user to install an RMM client or run a command that prints credential material. The approach is low-noise and often leaves no file-based indicators on endpoints, which is why defenders need telemetry on authentication flows and token issuance, not just endpoint binaries.
-
Narrative control and recruitment: Beyond pure intrusion, the actors use public channels to shape expectations: after high-profile events (e.g., CrowdStrike), they posted denials/clarifications aimed at minimizing forensic attribution while simultaneously using the publicity to recruit insiders. This is a deliberate method: by controlling the story they reduce investigatory clarity and increase the perceived value of insider partnerships, turning press attention into an asset for scaling future operations.
Victimology
-
SaaS & CRM ecosystems: Salesforce customers, vendors that integrate with Salesforce (Gainsight, Salesloft, Drift, Klaviyo). Google Threat Intelligence and multiple vendors reported hundreds of affected Salesforce instances following token misuse / Gainsight activity.
-
Large commercial sectors (preferred): aviation (Qantas, Hawaiian, WestJet reporting in CTI), insurance (Aflac, Philadelphia Insurance, Erie Insurance), retail and luxury brands (Dior, Adidas, Cartier), hosting providers and MSPs. Telegram recruitment posts explicitly list these sectors as targets (5-Eyes geos prioritized).
-
High-value individual accounts / celebrities: community chat banter and prior incidents indicate attacks on high-value individuals (crypto accounts, sports figures), though core business is enterprise data extortion.
Tools
-
RMM / remote tools: ScreenConnect, AnyDesk, TeamViewer, Splashtop, ConnectWise (explicitly discussed in chats).
-
Phishing / reverse proxy kits: custom phishing kits / staged SSO portals (Okta/Azure/Salesforce); hosting on privacy-friendly/vps providers (reported in vendor CTI).
-
RaaS families / encryptors: ShinySp1d3r (newly advertised/observed in samples uploaded to VirusTotal / discussed in Telegram), DragonForce (ESXi-focused strains) in RaaS/locker context. Broadcom and other vendors have posted initial ShinySp1d3r detections/analysis.
-
Living-off-the-land & AD tooling: PowerShell, AD enumeration scripts, WMIC/WMI, remote AD tools (mentioned in CTI).
MITRE ATT&CK TTPs
|
Tactic |
Technique ID |
Technique Name |
|
Reconnaissance
|
T1592 |
Gather Victim Identity Information |
|
T1597 |
Search Closed Sources |
|
|
T1595 |
Active Scanning |
|
|
Resource Development
|
T1585.001 |
Obtain Account (Email) |
|
T1585.002 |
Obtain Account (Social Media/Telegram) |
|
|
T1583.001 |
Acquire Infrastructure (VPS) |
|
|
T1583.006 |
Acquire Infrastructure (Botnet/RMM abuse) |
|
|
T1587.001 |
Develop Capabilities (Malware) |
|
|
T1588.002 |
Obtain Capabilities (Software) |
|
|
Initial Access
|
T1078 |
Valid Accounts |
|
T1078.004 |
Valid Accounts (Cloud) |
|
|
T1566.002 |
Spearphishing via Service |
|
|
T1566.004 |
Spearphishing (Voice/Vishing) |
|
|
T1621 |
Multi-Factor Authentication Request Generation (MFA Fatigue) |
|
|
T1190 |
Exploit Public-Facing Application |
|
|
T1133 |
External Remote Services |
|
|
T1098 |
Account Manipulation |
|
|
T1650 |
Account Access Removal |
|
|
Execution
|
T1059.001 |
PowerShell |
|
T1059.003 |
Windows Command Shell |
|
|
T1106 |
Native API |
|
|
Persistence
|
T1136.002 |
Create Cloud Account |
|
T1547.001 |
Registry Run Keys/Startup Folder |
|
|
T1505.003 |
Web Shell |
|
|
T1078 |
Valid Accounts |
|
|
Privilege Escalation |
T1548.002 |
Abuse Elevation Control Mechanism |
|
T1068 |
Exploitation for Privilege Escalation |
|
|
Defense Evasion
|
T1562.001 |
Disable or Modify Security Tools |
|
T1027 |
Obfuscated/Encrypted Files |
|
|
T1070.004 |
File Deletion |
|
|
T1036 |
Masquerading |
|
|
T1218 |
Signed Binary Proxy Execution |
|
|
T1564.003 |
Hidden Files & Directories |
|
|
Credential Access
|
T1556.006 |
Modify Authentication Process (SSO Interception) |
|
T1552.001 |
Credentials in Files |
|
|
T1555.003 |
Credentials from Web Browsers |
|
|
T1110.003 |
Password Spraying |
|
|
T1110.001 |
Credential Guessing |
|
|
Discovery
|
T1087.001 |
Account Discovery (Local/AD) |
|
T1069.002 |
Permission Groups Discovery |
|
|
T1046 |
Network Scanning |
|
|
T1082 |
System Information Discovery |
|
|
T1518.001 |
Security Software Discovery |
|
|
Lateral Movement |
T1021.001 |
Remote Services: RDP |
|
T1021.004 |
Remote Services: SSH |
|
|
T1570 |
Lateral Tool Transfer |
|
|
T1563.002 |
RDP Hijacking/Relay |
|
|
Collection
|
T1530 |
Data from Cloud Storage |
|
T1114 |
Email Collection |
|
|
T1005 |
Data from Local System |
|
|
Exfiltration
|
T1041 |
Exfiltration Over Command and Control Channel |
|
T1567.002 |
Exfiltration to Cloud Storage |
|
|
T1020 |
Automated Exfiltration |
|
|
Impact
|
T1486 |
Data Encrypted for Impact |
|
T1490 |
Inhibit System Recovery |
|
|
T1491.002 |
Defacement (Messaging/Extortion Notes) |
Recommendations
-
Revoke and rotate all affected integration tokens & OAuth grants: follow Salesforce/third-party vendor advisories. Monitor refresh token use and anomalous client IDs.
-
Hunt for insider indicators: search for external screenshot sharing, unusual off-hours RDP/AnyDesk sessions, VPN sessions originating from unusual IPs, and evidence of employee DMs with known handles (e.g., @SLSHsupport) in corporate Slack/Outlook logs where permitted. Your Telegram exports show actors demanding screenshots/AD commands as proof — hunt for those patterns.
-
Lock down consent grants for third-party apps: apply least-privilege permissions for connected apps, use app allowlists, and enable OAuth grant review workflows.
-
Strengthen SSO posture: require phishing-resistant MFA (hardware keys or platform MFA), reject push approvals where possible, and implement MFA MFA-challenge rate-limiting and anomalous approval detection.
-
Monitor RMM tool deployment & use: log and alert on new ScreenConnect/AnyDesk installations, and block unmanaged installs via application allowlisting. Chats show ScreenConnect use and requests for AV bypasses.
-
Insider risk program: build a cross-functional insider risk playbook that includes HR/legal coordination, auditing of privileged remote access, and a secure channel for employees to report coercion. SLSH explicitly markets “we pay insiders” in their channel.
-
Supply-chain / SaaS risk assessments: identify critical third-party apps with broad read privileges and require continuous attestation and vendor security controls (SAST, secrets management, least privilege).
Conclusion
Scattered Spider’s evolution into the SLSH ecosystem demonstrates a strategic shift away from purely noisy SIM-swap tricks toward identity-centric, supply-chain and insider-enabled intrusions paired with public extortion theatre. The November 2025 events (CrowdStrike insider screenshots; Salesforce/Gainsight “unusual activity” and token revocations) illustrate the potency and scalability of this model: one compromised third-party or one recruited insider can cascade across hundreds of customer orgs. Defenders must therefore complement endpoint-centric controls with SSO/OAuth hardening, RMM governance, and a mature insider-risk program.