
215 Victims and Growing: NightSpire’s Rapid Rise in the Ransomware Landscape
Executive Summary
NightSpire is an active ransomware operation first observed in February 2025, with at least 215 victims across North America, Europe, Asia-Pacific, the Middle East, and Africa. Likely a rebrand of the earlier Rbfs ransomware operation, the group employs a double-extortion strategy—combining data theft with file encryption—and operates dedicated data leak sites (DLS) on the dark web to pressure victims through public exposure and countdown timers. NightSpire demonstrates globally distributed, opportunistic targeting, with the highest concentration of victims in the United States and notable activity across APAC and Europe, primarily impacting manufacturing, technology, and healthcare sectors, while a significant proportion of victims remain unattributed.
Threat Profile
Group Overview
NightSpire first appeared on February 17, 2025, and remains active as of the time of creation of this report, with 215 victims listed on its leak site. The group employs a double-extortion model, encrypting victim data while simultaneously threatening to leak stolen information if ransom demands are not met. Targets are overwhelmingly concentrated among small to mid-size enterprises (SMEs) lacking mature security programs.
Attribution evidence strongly suggests NightSpire is a rebrand of the Rbfs ransomware operation. Shared infrastructure, overlapping victims listed on both groups' leak sites, and the simultaneous cessation of Rbfs activity coinciding with NightSpire's launch support this assessment.
Operational Characteristics
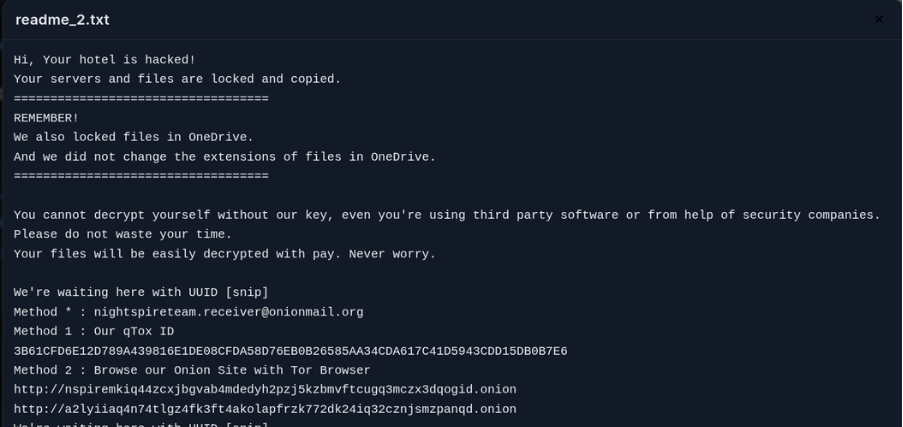
NightSpire's attacks follow a structured three-phase lifecycle: initial access via exploitation of public-facing infrastructure, lateral movement and credential harvesting using LOLBins, and a staged exfiltration-then-encryption chain. The Go-based payload uses RC4 and XOR obfuscation and implements a hybrid encryption strategy — block-level encryption for large files and full encryption for all others — with extended sleep intervals between operations to evade real-time detection. Notably, NightSpire also encrypts files stored in OneDrive cloud storage without altering file extensions, making cloud-side compromise significantly harder to detect.
Victimology
Overview
-
Total Victims: 215
-
Countries Affected: 48+
-
Active Since: Feb 2025 (~13 months)
-
Leak Site: Active
Geographical Distribution
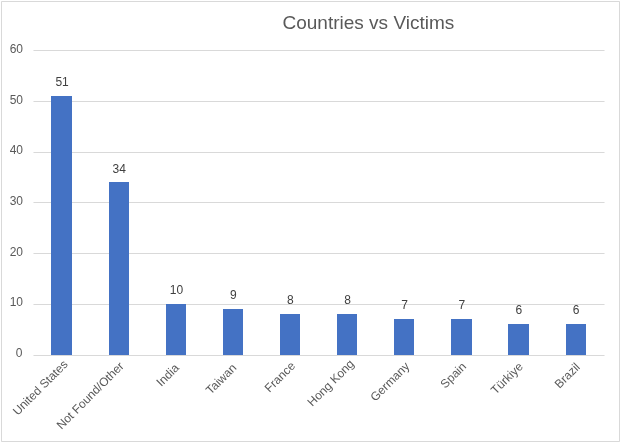
NightSpire has a strongly global victimology, spanning North America, Europe, Asia-Pacific, the Middle East, Latin America, and Africa. The United States accounts for the largest share with 51 confirmed victims, reflecting the group's opportunistic exploitation of exposed SME infrastructure in high-value Western economies. Significant APAC targeting is evident, with India (10), Taiwan (9), Hong Kong (8), and Japan (6) among the most affected. European targets are widely distributed across France, Germany, Spain, the United Kingdom, and Italy. A further 34 victims lacked confirmed country attribution.
Sector Targeting
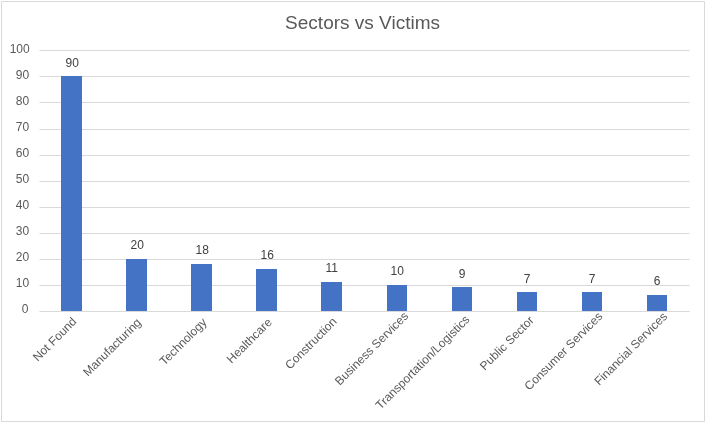
Among identified industries, Manufacturing leads with 20 confirmed victims, followed closely by Technology (18) and Healthcare (16). Construction (11) and Business Services (10) represent a notable focus on operational sectors often characterized by weaker cybersecurity postures. Transportation/Logistics (9), Public Sector (7), Consumer Services (7), and Financial Services (6) round out the top verticals. A significant portion — 90 victims — lacked sector attribution, suggesting either limited victim disclosure or incomplete intelligence visibility. The overall distribution reflects opportunistic rather than sector-specific targeting.
Technical Analysis
Initial Access and Foothold
NightSpire's primary and most documented initial access vector is exploitation of CVE-2024-55591, a critical authentication bypass vulnerability in Fortinet FortiOS and FortiProxy. The flaw allows unauthenticated attackers to obtain super-admin privileges via crafted requests. Active exploitation occurred even before public disclosure.
Secondary access vectors include:
-
RDP brute-force and credential stuffing
-
Phishing campaigns
-
MFA fatigue attacks
-
Exploitation of other vulnerable appliances
-
MSP compromise
Privilege Escalation, Defense Evasion, and Persistence
Following initial access, operators perform reconnaissance using tools like Everything.exe and Advanced IP Scanner, then escalate privileges using Mimikatz.
Key techniques include:
-
LOLBins (PowerShell, PsExec, WMI)
-
Obfuscation (RC4/XOR)
-
Registry persistence (Run keys)
-
Scheduled tasks
-
AnyDesk deployment
-
Account creation on compromised systems
Lateral Movement, Exfiltration, and Encryption
Lateral movement methods:
-
RDP
-
SMB / PsExec
-
WMI
Attack sequence:
-
Staging — File discovery and staging
-
Archiving — Compression using 7-Zip
-
Exfiltration — WinSCP, MEGACmd, Rclone
-
Encryption — .nspire extension + ransom note
Encryption:
-
Hybrid AES-256 + RSA-2048
-
Block-level encryption for large files
-
OneDrive files encrypted without extension change
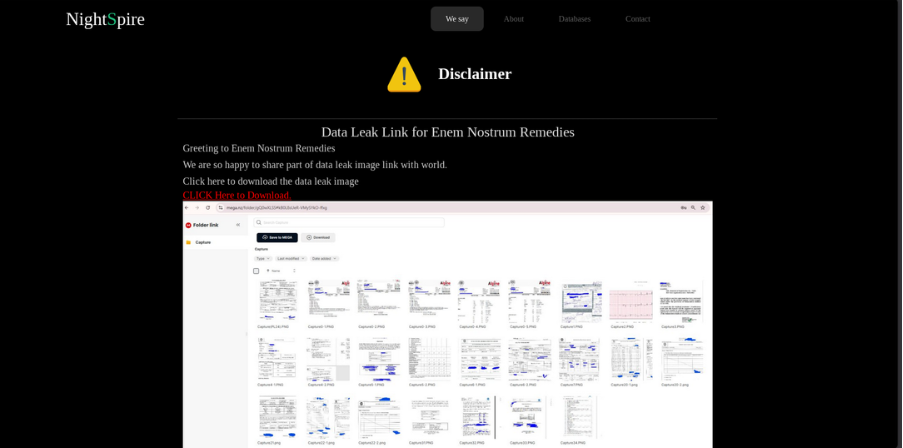
Data Leak Site (DLS)
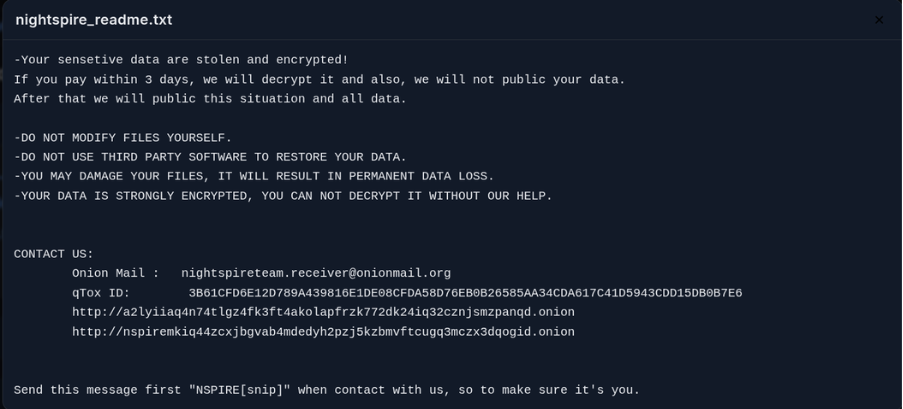
Ransom Note
MITRE ATT&CK TTPs
|
Tactic |
Technique ID |
Technique Name |
|
Resource Development |
T1587 |
Develop Capabilities |
|
Resource Development |
T1587.001 |
Develop Capabilities: Malware |
|
Initial Access |
T1190 |
Exploit Public-Facing Application (CVE-2024-55591) |
|
Initial Access |
T1078 |
Valid Accounts |
|
Initial Access |
T1110 |
Brute Force (RDP credential stuffing, MFA fatigue) |
|
Initial Access |
T1566 |
Phishing |
|
Execution |
T1059 |
Command and Scripting Interpreter: PowerShell / Windows Command Shell |
|
Execution |
T1072 |
Software Deployment Tools (PsExec, WinSCP, MEGACmd, 7-Zip) |
|
Persistence |
T1136 |
Create Account (FortiGate admin accounts) |
|
Persistence |
T1547.001 |
Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
|
Persistence |
T1053 |
Scheduled Task/Job |
|
Privilege Escalation |
T1068 |
Exploitation for Privilege Escalation (FortiOS super-admin via CVE-2024-55591) |
|
Defense Evasion |
T1036 |
Masquerading (renamed processes, legitimate tool abuse) |
|
Defense Evasion |
T1218 |
System Binary Proxy Execution (LOLBins) |
|
Defense Evasion |
T1027 |
Obfuscated Files or Information (RC4/XOR payload obfuscation) |
|
Defense Evasion |
T1070 |
Indicator Removal (log manipulation, temp file cleanup) |
|
Credential Access |
T1003 |
OS Credential Dumping (Mimikatz) |
|
Credential Access |
T1003.001 |
OS Credential Dumping: LSASS Memory |
|
Credential Access |
T1552 |
Unsecured Credentials |
|
Discovery |
T1046 |
Network Service Discovery (Advanced IP Scanner) |
|
Discovery |
T1057 |
Process Discovery |
|
Discovery |
T1082 |
System Information Discovery |
|
Discovery |
T1083 |
File and Directory Discovery (Everything.exe) |
|
Lateral Movement |
T1021.001 |
Remote Services: Remote Desktop Protocol |
|
Lateral Movement |
T1021.002 |
Remote Services: SMB/Windows Admin Shares (PsExec) |
|
Lateral Movement |
T1047 |
Windows Management Instrumentation (WMI) |
|
Collection & Exfiltration |
T1119 |
Automated Collection |
|
Collection & Exfiltration |
T1560.001 |
Archive Collected Data: Archive via Utility (7-Zip) |
|
Collection & Exfiltration |
T1567.002 |
Exfiltration Over Web Service: Exfiltration to Cloud Storage (MEGACmd, Rclone) |
|
Command & Control |
T1071 |
Application Layer Protocol: Web Protocols |
|
Command & Control |
T1219 |
Remote Access Software (AnyDesk) |
|
Impact |
T1486 |
Data Encrypted for Impact (.nspire extension; hybrid AES-256/RSA-2048) |
Indicators of Compromise
SHA-256:
- e275b8a02bf23b565bdaabadb220b39409eddc6b8253eb04e0f092d697e3b53d
-
4cda6af63873eca99b9a0b69be1c8b9c81b501339f569a30fd30394fa54da3e1
-
d5f9595abb54947a6b0f8a55428ca95e6402d2aeb72cbc109beca457555a99a6
-
32e10dc9fe935d7c835530be214142041b6aa25ee32c62648dea124401137ea5
E-Mail Address:
- night[.]spire[.]team[@]gmail[.]com
-
night[.]spire[.]team[@]proton[.]me
-
night[.]spire[.]team[@]onionmail[.]org
-
nightspireteam[.]receiver[@]proton[.]me
-
nightspireteam[.]receiver[@]onionmail[.]org
Mitigations & Recommendations
1. Patch Management & Perimeter Security
-
Apply patches for FortiOS/FortiProxy appliances immediately, prioritizing CVE-2024-55591
-
Restrict management-plane access using VPNs, IP allow-listing, and disable direct internet exposure
-
Regularly assess external attack surface to identify exposed RDP, VPN, and web services
2. Identity & Access Security
-
Enforce multi-factor authentication (MFA) for all remote and administrative access
-
Implement strong password policies and monitor for brute-force or credential-stuffing attacks
-
Audit privileged accounts regularly and enforce least-privilege access (RBAC)
3. Network Segmentation & Lateral Movement Control
-
Segment critical systems and restrict RDP, SMB, and WMI access to controlled hosts
-
Limit east-west traffic using firewall rules and network access controls
-
Monitor for anomalous lateral movement (e.g., unusual RDP sessions, PsExec activity)
4. Endpoint Protection & Behavioral Detection
-
Deploy EDR/XDR to detect LOLBin abuse (PowerShell, PsExec, WMI)
-
Monitor execution of tools like WinSCP, MEGACmd, Rclone, and 7-Zip on servers
-
Create alerts for abnormal processes, registry persistence, and large outbound data transfers
5. Data Protection & Backup Strategy
-
Maintain offline, immutable backups isolated from production environments
-
Regularly test backup restoration to ensure recovery readiness
-
Monitor for large-scale data staging, compression, and exfiltration activity
6. Threat Detection & Intelligence Integration
-
Integrate IOCs and MITRE ATT&CK mappings into SIEM/XDR systems
-
Conduct threat hunting for early indicators like FortiGate compromise and credential abuse
-
Monitor evolving ransomware infrastructure using threat intelligence feeds
7. Security Awareness & Incident Preparedness
-
Train users to recognize phishing and credential theft attempts
-
Develop and rehearse ransomware-specific incident response plans
-
Coordinate with external IR teams and legal authorities for rapid response
Conclusion
NightSpire has rapidly established itself as a persistent and globally active ransomware threat within approximately 13 months of emergence. With over 215 victims across more than 48 countries, the group poses a significant risk to SMEs worldwide.
Despite operational weaknesses, its reliance on legitimate administrative tools makes detection difficult. Organizations must focus on:
-
Patch management
-
Identity security
-
Behavioral monitoring
-
Backup resilience
The most effective defense remains early detection of pre-encryption activity, particularly FortiGate compromise and data exfiltration behaviors.