Massive "Finastra" Data Breach: Key Lessons from the 400GB Data Exposure Attack
In recent cybersecurity news, Finastra, one of the world’s largest financial services software providers, suffered a significant data breach that has raised alarms across the industry. The breach, which exposed a staggering 400GB of sensitive data, was reportedly executed via stolen credentials, highlighting the ongoing vulnerability of businesses to credential-based attacks. In this blog, we’ll delve into the details of the Finastra data breach, its impact, and the key lessons organizations can learn from this attack.
Finastra, which provides financial technology solutions to banks, credit unions, and other financial institutions, recently disclosed a significant data breach that saw over 400 gigabytes of sensitive data stolen from its Secure File Transfer Platform (SFTP). The cybercriminal behind the breach, known as "abyss0," reportedly began selling the stolen data on the dark web, raising concerns about credential security and the importance of proactive monitoring for exposed information.
How the Breach Unfolded
On November 7, 2024, Finastra’s Security Operations Center (SOC) detected suspicious activity on its internally hosted SFTP platform, which the company uses to send files securely. Upon discovery, the platform was promptly isolated, and Finastra activated its incident response protocols to contain the threat.
The following day, November 8, a cybercriminal publicly claimed on the dark web that they had exfiltrated data from Finastra. The stolen files reportedly included sensitive information belonging to some of the firm’s largest banking clients.
Finastra’s Investigation and Findings
Finastra responded swiftly by isolating the compromised platform and engaging Sygnia, a leading cybersecurity firm, to conduct a forensic investigation.
Key findings so far include:
Stolen Credentials: Initial evidence indicates that compromised credentials were used to access the platform.
No Malware: The attacker did not deploy malware or tamper with customer files.
Limited Scope: No evidence suggests the attacker moved laterally within Finastra’s network.
Focused Breach: Only exfiltrated files were accessed; no other files were viewed.
The cybercriminal behind this breach, using the alias "abyss0," has a history of selling stolen data.
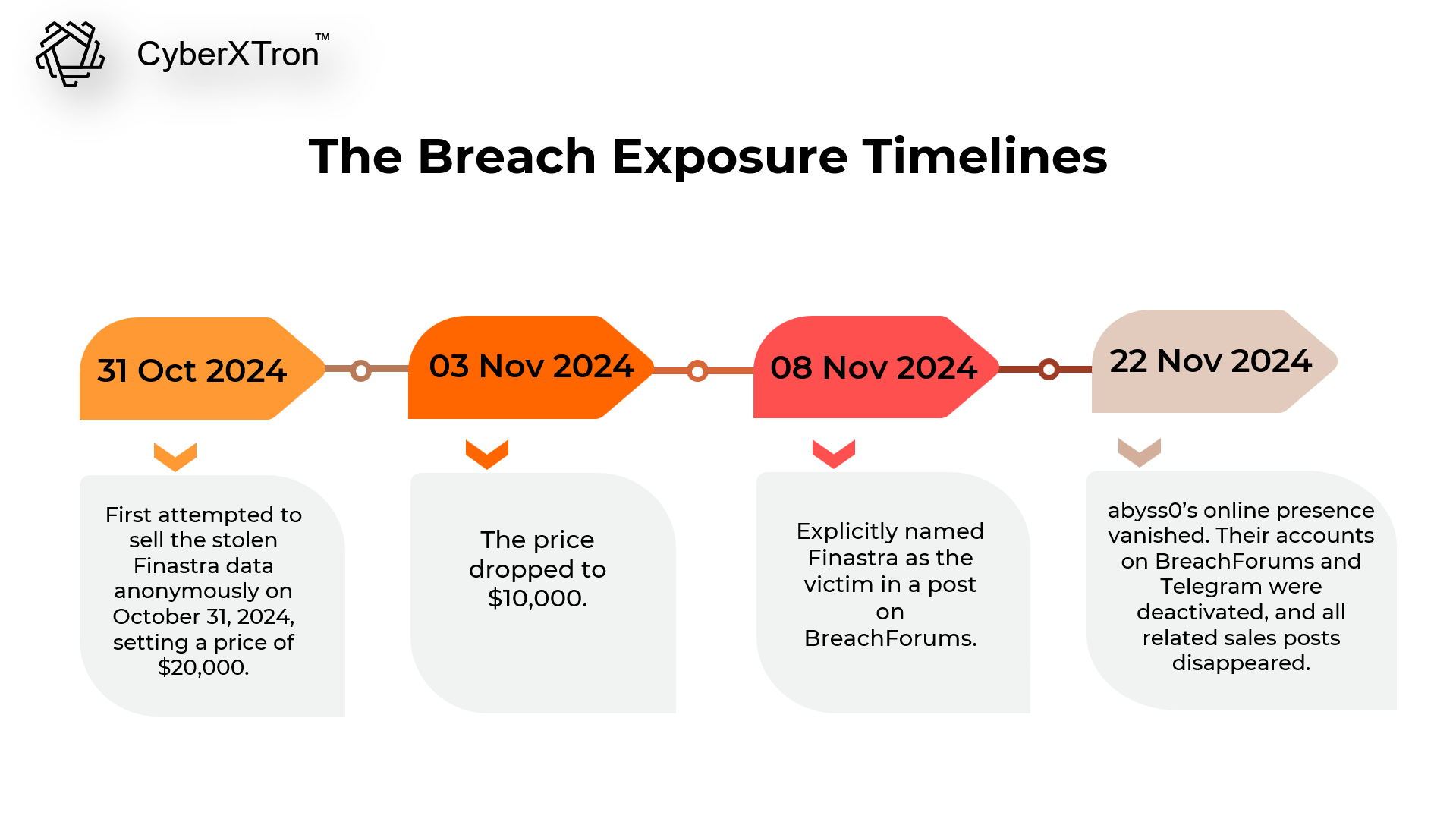
They first attempted to sell the stolen Finastra data anonymously on October 31, 2024, setting a price of $20,000.
By November 3, the price dropped to $10,000.
On November 8, they explicitly named Finastra as the victim in a post on BreachForums.
Shortly after, abyss0’s online presence vanished. Their accounts on BreachForums and Telegram were deactivated, and all related sales posts disappeared. Whether the disappearance was triggered by the sale of the data, external pressure, or an attempt to avoid attention is unclear.
Lessons Learned: The Importance of Proactive Credentials Leak Monitoring
The Finastra breach underscores the risks of stolen credentials and highlights why credential leak monitoring should be a critical component of any cybersecurity strategy.
Here’s how continuous proactive credentials leak monitoring solutions can help mitigate threats:
- Early Detection: Identifying compromised credentials on the deep/dark web gives organizations a critical window to neutralize risks before attackers exploit them.
- Insight Into Threat Actor Behavior: Dark web monitoring provides visibility into how attackers are obtaining and using stolen data. This intelligence can guide improvements in phishing awareness and access controls.
- Continuous Monitoring for Persistent Threats: Threat actors often resell or repost data. Ongoing monitoring ensures organizations can detect repeat listings or new threats tied to older breaches.
- Integration With Incident Response Plans: Combine data leak monitoring intelligence with your incident response strategy to improve readiness and reduce response times during breaches.
- Risk Reduction: Prevent unauthorized logins or privilege escalation stemming from compromised accounts.
Mitigation Strategies
- Implement Deep/Dark Web Monitoring Solution: Leverage advanced tools and services to scan dark web forums, marketplaces, and repositories for stolen credentials or sensitive data tied to your organization.
- Set Up Automated Alerts: Use automated systems to alert your team when your organization’s credentials are detected on the dark web, enabling swift action to mitigate risks.
- Strengthen Authentication Practices: Enforce MFA across all critical systems to minimize the impact of compromised credentials. Encourage the use of strong, unique passwords and regular updates.
- Conduct Regular Credential Audits: Review account access logs for unusual activity. Audit privileged accounts and restrict access to essential personnel only.
The Bigger Picture
The Finastra breach underscores the growing threat of credential-based attacks. As dark web markets continue to thrive, organizations must recognize the critical importance of monitoring and securing exposed credentials to stay ahead of cybercriminals.
CyberXTron offers a continuous monitoring solution that scans a vast array of deep and dark web forums, marketplaces, and cybercriminal networks. We provide instant alerts on stolen credentials and sensitive data breaches. Feel free to reach out to our support team to perform a quick digital risk assessment.
By combining advanced monitoring tools with robust security practices, organizations can significantly reduce the risks posed by stolen credentials.
Stay secure and stay vigilant. If you’re looking for more information or would like to schedule a demo, contact us today at support@cyberxtron.com or https://cyberxtron.com/contact-us