
Exploiting CVE-2025-56383 — CyberXTron PoC Demonstrates Notepad++ DLL Hijack
Executive summary
On 26th September, 2025 CVE-2025-56383 was published describing a DLL hijacking issue affecting Notepad++ v8.8.3. The publicly posted proof-of-concept demonstrates replacing a plugin DLL with a malicious DLL that forwards exports to the original library while executing injected code; when Notepad++ is launched the forged DLL runs. Several vulnerability trackers and security vendors recorded the report, and discussion in the community notes the exploit requires the affected binary (or its plugin folder) to be writable by an unprivileged actor — making the real-world severity dependent on installation and filesystem permissions.
Affected Version:
CVE-2025-56383 impacts Notepad++ installations and has been publicly reported against the Notepad++ release v8.8.3.
Vulnerability details:
Root Cause:
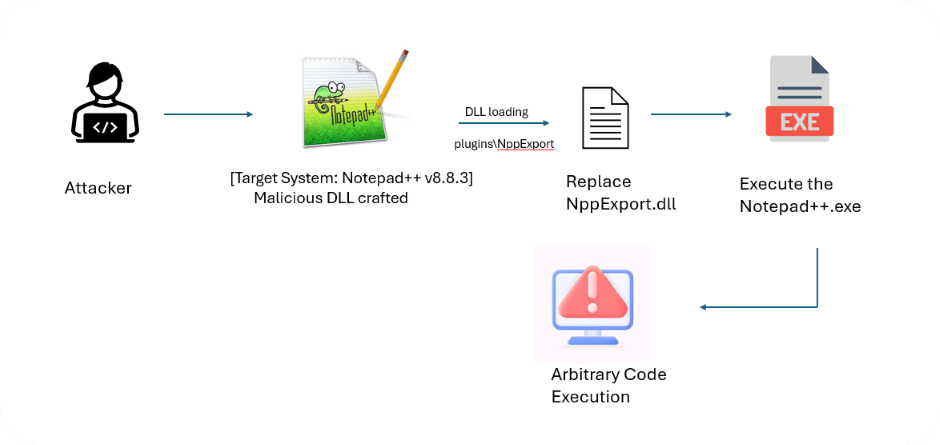
CVE-2025-56383 exists due to a classic DLL search-order and load-time substitution vulnerability combined with environments where Notepad++ plugin folders are writable by non-privileged users. The vulnerability arises from Notepad++'s mechanism of loading plugin DLLs from predictable subfolders (e.g., plugins\NppExport). If an attacker can write a DLL with the same filename into the plugin folder (or replace an existing DLL), Windows will load that DLL into the notepad++.exe process. The forged DLL can forward expected exports to the original binary to preserve normal application behavior while executing arbitrary code during load.
In a custom proof-of-concept, this behavior was weaponized by replacing the legitimate NppExport.dll with a malicious version in a lab VMware Windows 10 environment. Upon launching Notepad++ v8.8.3, the malicious DLL executed a payload that displayed a message box with the text "DLL hijacking test”. This demonstrates that arbitrary code execution can be achieved using a tampered plugin directory.By leveraging this primitive, an attacker could escalate the impact further, for example:
- Injecting persistent malicious code (e.g., a reverse shell or keylogger) into the DLL, leading to sustained remote code execution (RCE) each time Notepad++ is launched.
- Modifying Notepad++ settings or related system files (e.g., registry entries) to redirect file operations or exfiltrate sensitive data, enabling stealthy data theft or persistence.
Key Contributing Factors:
- Plugins are discovered and loaded from application subfolders with predictable names (e.g., plugins\NppExport).
- Installations placed in user-writable locations (e.g., user profile, %APPDATA%, or other non-protected folders) make it possible for unprivileged accounts to drop or replace DLLs.
- No integrity verification (signature or checksum) on plugin DLLs at load time in the tested configuration.
Exploitation Flow:
Exposure & risk
Exploitation Preconditions:
- Local file-write access to Notepad++ plugin or installation folder.
- A victim (or process) that launches notepad++.exe after the malicious DLL is placed.
Common situations that increase exposure:
- User-level installs (installing Notepad++ under %USERPROFILE% or similar locations).
- Shared workstations where multiple users have write privileges to application directories.
- Misconfigured enterprise imaging/provisioning that leaves install folders writable.
Stealth factor:
High 8.4 — the attack can be triggered by ordinary application start and, with export forwarding, the application appears to behave normally. A malicious DLL that proxies exports to the original will not disrupt standard functionality, making casual detection less likely.
Proof-of-Concept and Active Exploitation:
Exploitation of CVE-2025-56383 is straightforward for an attacker but difficult for a victim to detect in real time. The vulnerability arises from a DLL hijacking flaw in Notepad++ v8.8.3, where the application fails to enforce secure DLL loading paths. This allows an attacker with write access to the installation directory to replace the legitimate NppExport.dll with a malicious version. The exploit hinges on Notepad++'s plugin loading mechanism, which does not validate the integrity or origin of DLLs in the plugins\NppExport folder, especially when installed in a writable directory (e.g., outside protected system paths like C:\Program Files).
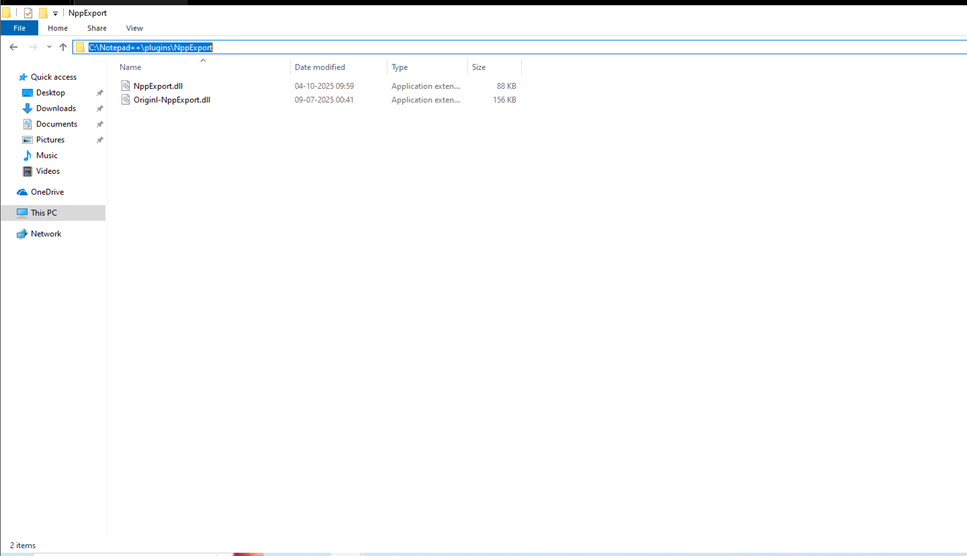
- Backing up the original NppExport.dll to original-NppExport.dll.
- Replacing it with the malicious NppExport.dll provided in the PoC.
- Launching Notepad++ v8.8.3, triggering the loading of the malicious DLL.
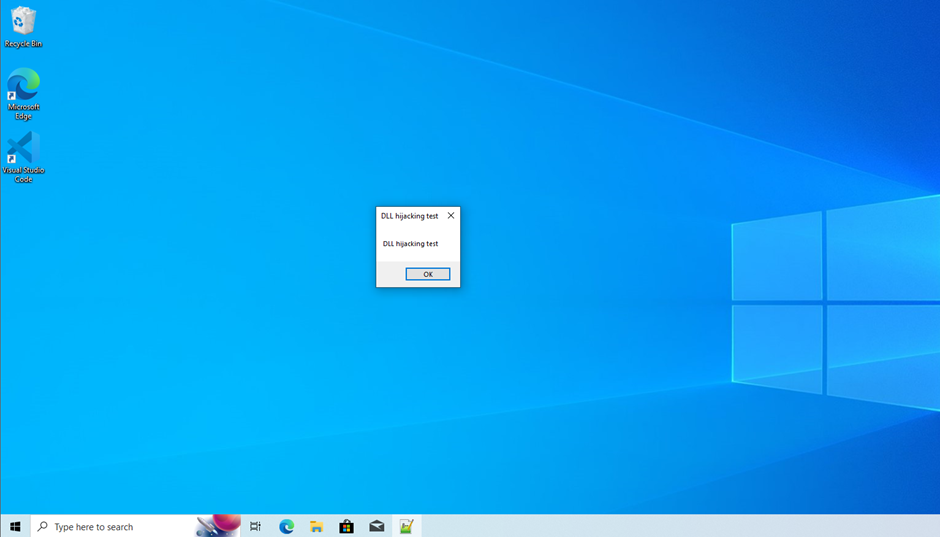
Upon execution, the malicious DLL's DllMain entry point was invoked, executing a payload that displayed a message box with the text "DLL hijacking test". This demonstrates that arbitrary code execution can be achieved simply by opening Notepad++ with the tampered plugin.
Once arbitrary code execution is achieved, attackers can escalate their access in multiple ways. One technique involves embedding a persistent payload in the DLL, such as a reverse shell or keylogger, which runs each time Notepad++ is launched. This transforms the initial hijack into sustained remote code execution (RCE) under the victim's user context. The screenshots provided confirm the successful replacement and execution, with file timestamps and sizes aligning with the PoC's design.
Another exploitation path is configuration tampering. By leveraging the DLL to modify Notepad++ settings or related system files (e.g., user preferences or registry entries), an attacker could redirect file operations or exfiltrate sensitive data (e.g., edited documents) to a remote server. Since Notepad++ operations would appear normal, the compromise remains stealthy, posing a risk of data leakage without user awareness.
Beyond individual systems, this vulnerability has supply chain implications. Many organizations deploy Notepad++ on developer or build machines where unprivileged users might install it in writable locations. If a malicious DLL is introduced via a trojanized plugin or shared directory, it could compromise build scripts, inject malicious code into software projects, or alter configuration files critical to pipeline integrity. The ease of delivery through phishing (e.g., sending a crafted plugin) or compromised updates amplifies the risk.
Mitigation
To address CVE-2025-56383, organizations should immediately upgrade Notepad++ to the latest patched release (≥ v8.8.4 or the version recommended by the vendor). Using older or unpatched versions, such as v8.8.3, exposes systems to potential exploitation. In addition, the following security measures are recommended:
- Apply Vendor Patch: Upgrade Notepad++ to a secure version released after the vulnerability disclosure.
- Restrict Write Access: Install Notepad++ in protected directories (e.g., C:\Program Files\Notepad++) where unprivileged users lack write permissions, preventing DLL replacement.
- Implement File System Monitoring: Monitor the plugins\NppExport directory and system logs for unexpected DLL modifications or execution attempts.
Timeline
Conclusion
The discovery of CVE-2025-56383 underscores how even widely used developer tools like Notepad++ can become significant attack vectors when flaws emerge. DLL hijacking vulnerabilities not only compromise system integrity but can also be leveraged for malicious code execution, malware delivery, and potential privilege escalation. Users and organizations must respond quickly—by applying the official patches, avoiding the use of vulnerable versions, and carefully vetting plugin sources before integration. Strengthening security through endpoint monitoring, supply chain risk management, and continuous vulnerability scanning is critical to detect abnormal DLL behaviors before exploitation occurs. Leveraging early threat intelligence, coordinated advisories, and proactive patch management helps reduce exposure. In today’s evolving threat landscape, maintaining vigilance and implementing layered security controls are essential to safeguard against exploitation of trusted tools like Notepad++.
At CyberXTron, we specialize in Autonomous Digital Risk Protection and AI-driven Threat Intelligence tailored for protection against hacktivist threats and targeted cyber-attacks.
Click here to Book a free consultation with our expert team!!!