CVE-2024-37798 - Cross-Site Scripting (XSS) in Beauty Parlour Management System
Title: CVE-2024-37798 - Cross-Site Scripting (XSS) in Beauty Parlour Management System
CVE_ID: CVE-2024-37798 Vendor: Phpgurukul Affected Product: Beauty Parlour Management System Affected Version/s: 1.0 Status: Pending Fix
Description: A newly discovered Cross-Site Scripting (XSS) vulnerability has been identified in the BPMS Admin Panel, specifically in the `search-appointment.php` endpoint. This vulnerability allows attackers to execute arbitrary JavaScript in the context of the user's browser, potentially leading to various malicious activities.
Proof of Concept (POC):
Target URL: `http://localhost/bpms/admin/search-appointment.php`
XSS Payload: <script>alert(1)</script>
Screenshots:
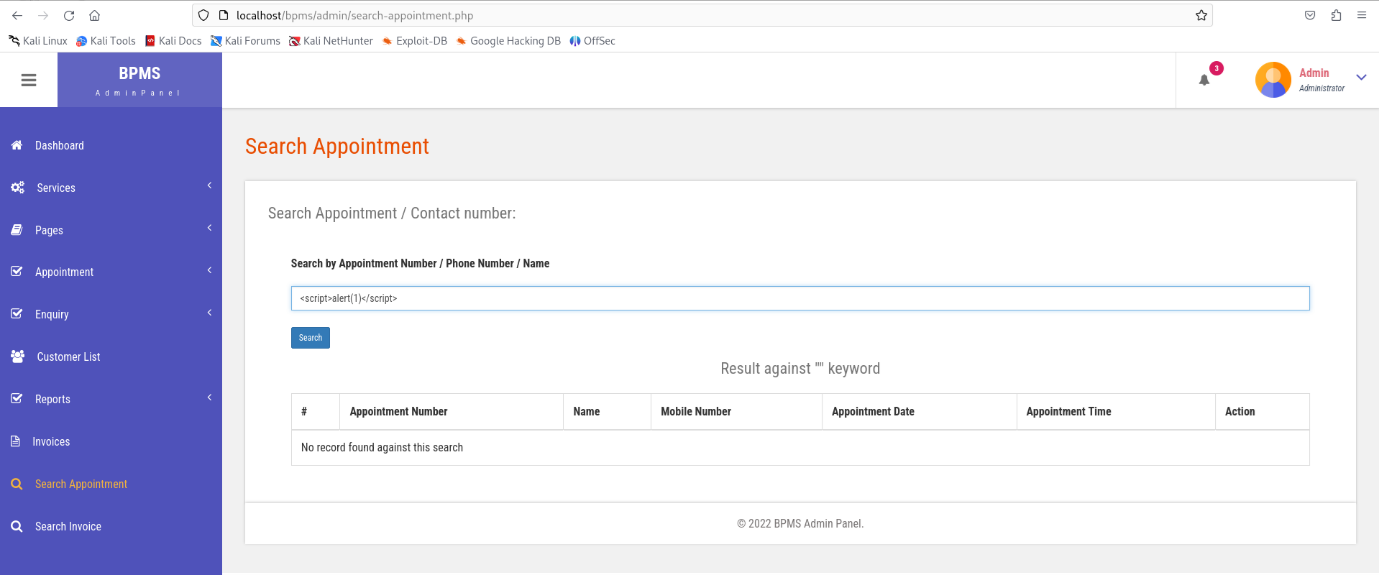
Fig 1: Injecting Payload into the Beauty Parlour Management System Admin Panel
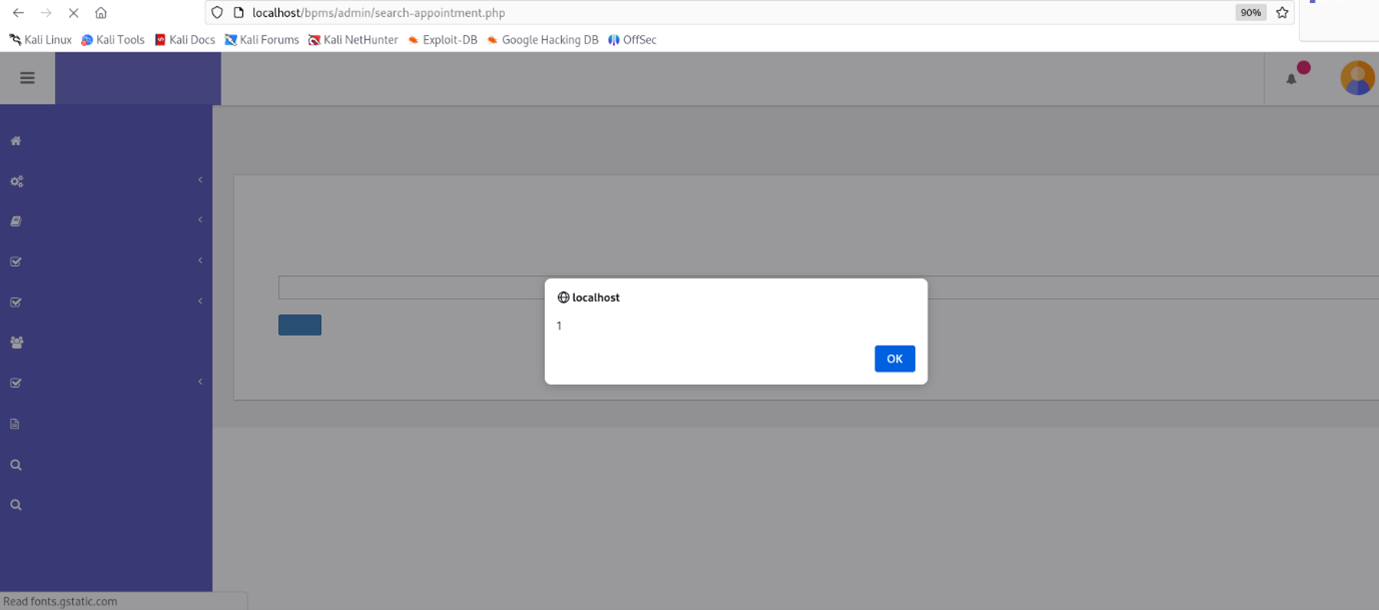
Fig 2
Steps to Reproduce:
- Navigate to the BPMS Admin Panel.
- Go to the search-appointment.php endpoint: http://localhost/bpms/admin/search-appointment.php.
- In the search input field, enter the XSS payload: <script>alert(1)</script>
- Submit the search form. Observe that an alert box displaying "1" is triggered, indicating the execution of the injected JavaScript code.
Impact:
If exploited, this XSS vulnerability can lead to:
- Unauthorized execution of scripts in the user's browser.
- Theft of sensitive information such as session cookies, which could lead to account hijacking.
- Redirection to malicious websites.
- Display of phishing content or other forms of social engineering attacks.
Remediations:
- Patch Availability: Currently, there is no official patch available. Users should check with the BPMS vendor for updates.
- Workarounds:
- Apply input validation and sanitization on all user inputs.
- Encode output to ensure that any data rendered in the browser is treated as text rather than executable code.
- Implement Content Security Policy (CSP) to limit the sources from which scripts can be executed.
- Best Practices:
- Regularly update and patch software.
- Use frameworks and libraries that automatically escape data to prevent XSS.
- Monitor and log unusual activities to detect and respond to potential attacks promptly.
Uncover hidden weaknesses before attackers do: Our elite Offensive Security Research Team relentlessly identifies and reports vulnerabilities in critical applications. Subscribe to our solutions and leverage this expertise to proactively fortify your defenses against ever-evolving cyber threats.
Explore our solutions on [https://cyberxtron.com/] or contact our support team at support@cyberxtron.com.